Your lease end date is fixed. Your carrier install date isn’t. The server closet still has equipment nobody wants to move, nobody wants to own, and nobody wants to be responsible for wiping. That’s where most IT office relocation services go sideways.
A clean move isn’t just a transportation project. It’s a coordinated cutover of infrastructure, security controls, telecom, inventory, compliance, and end-of-life assets. Teams that treat relocation like furniture moving usually discover significant problems after the trucks leave.
The practical fix is to run the move like an IT program, not a facilities task. That means locking scope early, auditing every asset, separating equipment that should move from equipment that should be destroyed or remarketed, and documenting chain of custody from disconnect through go-live.
Building Your Relocation Blueprint
Internal teams often underestimate how hard the planning stage is. Research found that 65% of organizations managing relocations internally perceived planning and building IT solutions as difficult, and it recommends a full IT audit 6 to 8 weeks before the move in the relocation management research.
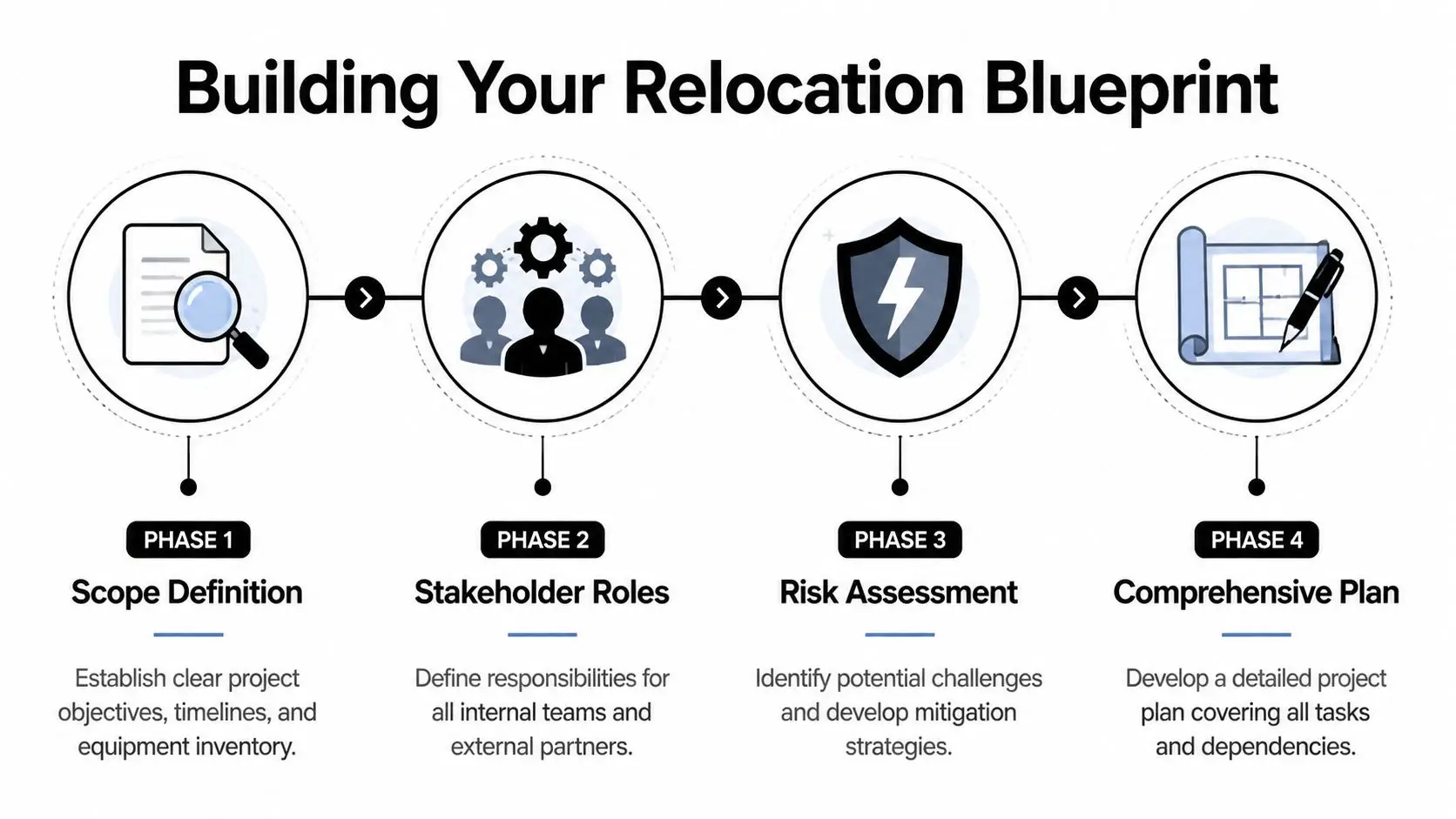
Start with the dependency map
The first useful document isn’t a moving checklist. It’s a dependency map that shows what has to happen, in what order, and who owns each step.
Include these workstreams:
- Network and telecom: Carrier turn-up, cabling, firewall cutover, wireless design, voice services
- Compute and storage: Server shutdown sequencing, virtualization dependencies, SAN or NAS handling, backup verification
- Facilities coordination: Power, cooling, rack placement, access control, loading dock rules, elevator windows
- User environment: Desktop moves, printer mapping, conference room systems, badge access, day-one support
- Disposition path: Retired laptops, decommissioned servers, failed drives, spare switches, leased returns
If your new site includes major connectivity changes, it helps to review understanding dark fibre options before you finalize transport and cutover assumptions.
Define roles before vendors start asking questions
Most delays happen because ownership is fuzzy. Facilities assumes IT is handling rack power. IT assumes the cabling vendor is labeling drops. Procurement assumes the mover is documenting serial numbers. Nobody is accountable.
A workable role chart usually assigns:
- IT project lead for scope, risk log, cutover plan, and test acceptance
- Facilities lead for site readiness, access windows, and landlord coordination
- Security or compliance lead for data handling, device release, and audit evidence
- Vendor manager for proposals, insurance, statements of work, and escalation paths
Practical rule: If a task affects uptime, data, or chain of custody, assign one owner and one backup owner by name.
Build the floor plan like an operations document
A relocation floor plan should do more than show where desks go. It needs server rack locations, cable routing, security integration points, power requirements, redundancy needs, and handoff zones for incoming and outgoing equipment.
That’s also the right stage to align relocation with broader IT asset lifecycle management. Equipment that’s near end of life shouldn’t automatically earn space in the new office.
Auditing Assets and Integrating Secure Disposal
Relocation plans frequently fail because teams inventory what they need to move, but they don’t classify what shouldn’t move.
That gap matters. A critical weakness in relocation planning is the failure to integrate secure ITAD. Unmanaged legacy assets can raise project costs by 15% to 25%, and 70% to 80% of relocations involve such equipment without a clear disposition plan, according to the office relocation project management guidance.

Separate move inventory from disposition inventory
A wall-to-wall audit should create four clear buckets:
| Category | What belongs there | What happens next |
|---|---|---|
| Move | Supported devices needed at the new site | Pack, track, reinstall |
| Replace | Aging assets being swapped during the move | Stage new gear, remove old gear securely |
| Return | Leased or vendor-owned equipment | Confirm contract return terms and evidence |
| Dispose or recover value | End-of-life devices, failed media, surplus stock | Wipe, shred, recycle, or remarket |
That classification has to happen before packing day. If you wait until the weekend of the move, old hardware gets shoved into staging rooms and forgotten.
Treat data destruction as a relocation task
Data-bearing equipment needs its own workflow. Laptops, desktops, servers, SAN shelves, backup appliances, copier drives, and removable media all need documented handling. For regulated organizations, that includes disposal steps that support the FTC Disposal Rule and internal security policies.
A practical sequence looks like this:
- Identify data-bearing assets: Don’t limit this to servers. Include workstations, network appliances, badge systems, multifunction devices, and retired spares.
- Choose the destruction method: Some assets can be sanitized for reuse. Others should go directly to shredding because of condition, policy, or risk.
- Preserve audit evidence: Record serial numbers, asset tags, custody transfers, and final certificates.
- Control release points: Only designated staff should authorize equipment leaving the site.
For organizations standardizing sanitization requirements, NIST SP 800-88 guidance is the benchmark many IT and compliance teams use to define acceptable media sanitization practices.
Legacy gear becomes dangerous when nobody owns the decision. The move manager assumes IT will handle it. IT assumes procurement already approved disposal. The devices sit in a closet with live data on them.
Physical security still matters during audit and staging
Asset control isn’t just a paperwork issue. Audit teams need secure staging zones, restricted access, tamper-resistant labeling, and documented handoffs. Broader principles from essential layers of asset protection apply well here because relocation exposure is physical as much as digital.
One practical note from field work: don’t stage retired drives beside active move inventory. Once those streams mix, tracking gets messy fast, and your destruction evidence gets harder to defend later.
Executing a Secure Physical Relocation
Move day rewards discipline, not improvisation. By the time disconnect starts, every asset should already be tagged as move, return, or disposition.

Protect the chain of custody
For high-value or data-bearing equipment, chain of custody starts the moment the device is unplugged. Use serialized inventory sheets, tamper-evident labels, sign-off logs, and controlled loading procedures.
A solid handoff process includes:
- Disconnect validation: Confirm hostname, serial, rack position, and destination status before removal
- Packaging control: Use packing that matches the asset type, especially for servers, storage, and fragile electronics
- Vehicle accountability: Log what went on which truck and who accepted custody
- Receiving confirmation: Match every unit against the outbound manifest before installation
Use specialists for de-install and transport
Generic office movers can handle desks. They usually aren’t built for blade chassis, storage arrays, telecom gear, or racks with strict handling requirements. For organizations that need coordinated de-installation, packing, transport, and documentation, office relocation movers for IT equipment is the kind of specialized service scope to evaluate.
A missing switch is annoying. A missing firewall, backup appliance, or drive array is a security incident until proven otherwise.
Keep the command structure simple
During the physical move, one person should run the bridge. That person tracks status, resolves exceptions, and controls release decisions. If field teams discover unlabeled equipment, they don’t guess. They escalate.
That discipline is what keeps relocation from turning into a scavenger hunt at the new site.
Go-Live Testing and Infrastructure Cutover
A relocation isn’t successful when the last pallet arrives. It’s successful when users can authenticate, connect, print, call, and reach business systems without hidden failure points.
The risk here is larger than many teams assume. As many as 40% of office moves face significant downtime, and failing to quantify risks such as Wi-Fi dead zones or insufficient telecom capacity can lead to 20% to 30% higher long-term operational costs from outages, according to the IT office relocation checklist analysis.

Test the site, not just the hardware
A server can boot normally while the office still fails operationally. Test by workflow, not by device alone.
Focus on:
- Connectivity paths: Wired ports, Wi-Fi coverage, VPN access, WAN failover, DNS reachability
- Business functions: ERP, file shares, VoIP, conferencing, badge systems, print services
- Environmental support: Rack power, cooling behavior, UPS status, telecom demarc readiness
- User experience: Conference rooms, guest Wi-Fi, remote worker access, mobile coverage in problem areas
Build a cutover with rollback in mind
The cleanest cutovers are phased. Core services go first. User groups follow in waves. Critical teams get higher-touch validation. If something fails, the rollback path has already been approved.
Power quality often gets less attention than network design. Before high-load systems are commissioned, it’s smart to review site readiness with facilities and, where needed, outside specialists familiar with preventative electrical services for operations.
Don’t accept “the internet is up” as a test result. Validate the actual workflows your finance, operations, support, and remote staff depend on.
Vendor Selection and Contract Essentials
The vendor list shapes the outcome more than the move checklist does. Good vendors reduce ambiguity. Weak vendors add meetings, excuses, and undocumented handoffs.
Technology-enabled relocation management is becoming standard. Companies using these platforms report a 40% to 60% reduction in IT equipment loss and faster audit processes, and the corporate relocation services market is projected to reach over USD 31.5 billion by 2032 in the market outlook on corporate relocation services.
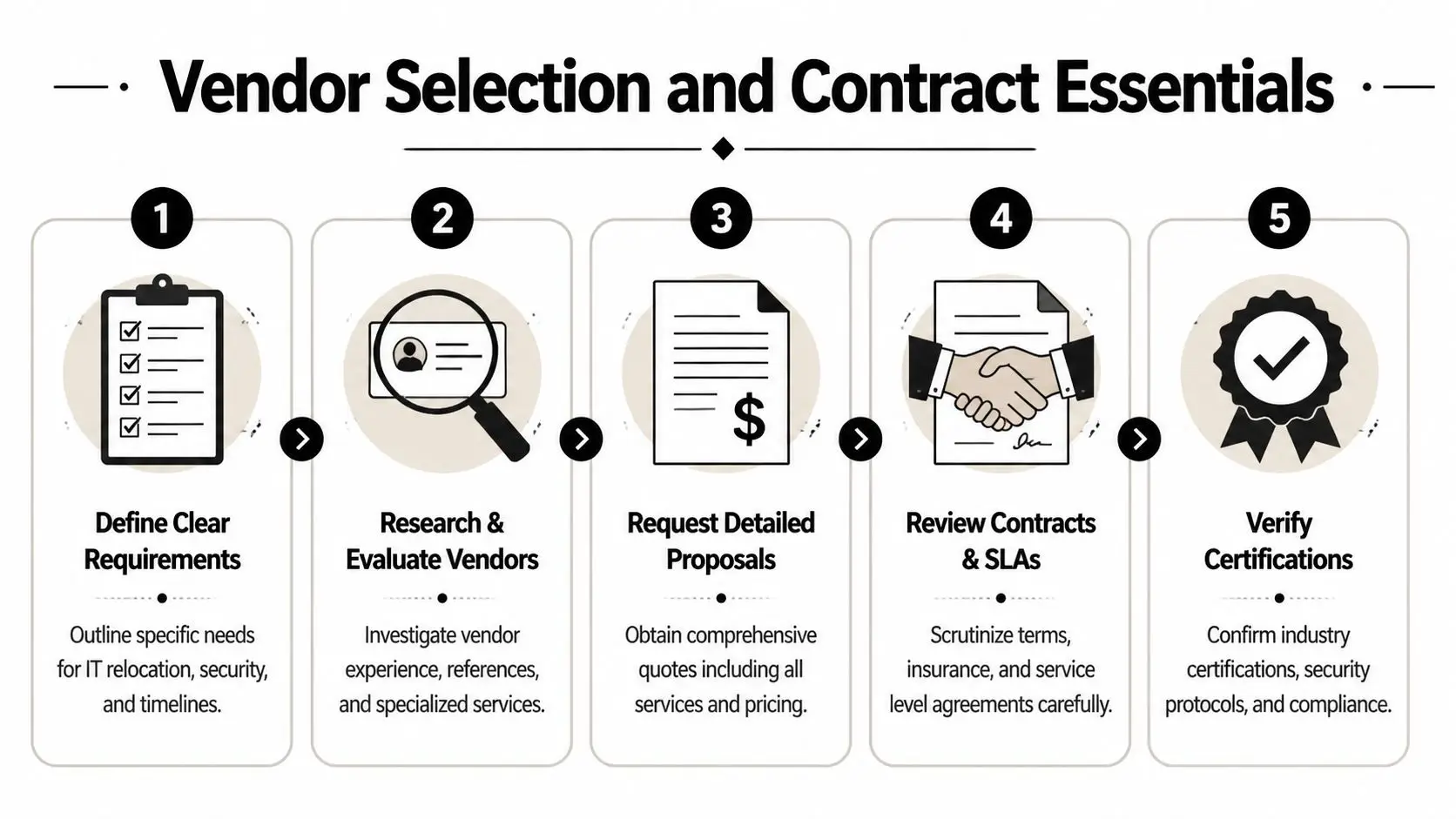
What your RFP should require
A relocation and ITAD RFP should ask for more than labor rates. It should force operational detail.
Ask vendors to define:
- Asset tracking method: Serial-level visibility, scan events, exception handling
- Data destruction process: Wiping, shredding, certificates, custody records
- Reporting outputs: Recycling certificates, destruction certificates, itemized disposition reports
- Integration capability: Whether status updates can feed enterprise systems or dashboards
- Insurance and compliance evidence: Transport, environmental handling, and service responsibility
A useful working reference is a structured vendor due diligence checklist that procurement, IT, and compliance can review together.
The contract terms that matter in practice
Some clauses sound administrative until a device goes missing. Then they become the whole story.
Insist on clear terms for custody transfer, incident reporting, serialized reconciliation, approved destruction methods, final reporting timelines, and responsibility for subcontractors. If a vendor uses downstream partners, that should be disclosed before award, not after pickup is scheduled.
One practical example: Beyond Surplus offers logistics-coordinated ITAD, secure data destruction, and certificates of recycling and data destruction that can fit into a relocation reporting workflow. That’s useful when retired assets need to leave the old site before the new office is live.
Adapting the Playbook for Specialized Facilities
A law office move and a hospital move might share trucks, labels, and floor plans. They do not share the same risk profile.
Data centers and high-availability environments
For a data center relocation, the tension is always between speed and control. Operations teams want the migration window short. Infrastructure teams want every power, cooling, and dependency issue validated before a single rack is touched.
In those projects, de-install sequencing matters as much as transport. Teams usually need rack diagrams, port maps, application dependencies, maintenance windows, rollback paths, and a controlled process for retired hardware that won’t be reinstalled. Where equipment is being removed permanently, data center decommissioning services often sit alongside the relocation work rather than after it.
Healthcare environments
Hospitals and clinics carry a different burden. Devices may hold patient data in obvious places, like workstations and servers, and in overlooked places, like imaging systems, copiers, specialty carts, and older embedded equipment. The relocation plan has to protect patient data, preserve custody records, and avoid casual device swaps that break validation or internal controls.
The practical adjustment is tighter segregation. Clinical systems, biomedical devices, admin systems, and retired media shouldn’t move through the same workflow just because they’re in the same building.
Schools and universities
Education environments create volume and variety. A single move might involve faculty laptops, classroom desktops, switches, lab gear, library systems, tablets, printers, and storage from old AV rooms. Student data protection sits in the background of all of it, even when the relocation appears routine.
The best approach is to standardize by device class, not by department. Lab equipment gets one process. User devices get another. Retired storage gets a locked destruction path. That keeps the project manageable when inventory is broad and ownership is spread across many stakeholders.
If your team is planning an office move and needs a secure path for surplus equipment, data destruction, and documented chain of custody, contact Beyond Surplus for certified electronics recycling and IT asset disposal.