Your lease is signed. Facilities is focused on furniture layouts. Leadership wants a move date that won’t disrupt revenue. IT gets the hard part: relocating the systems people depend on, deciding what equipment is worth moving, and making sure no retired device leaves with recoverable data still on it.
That’s why standard office moving checklists usually fail IT directors. They treat the move like a packing problem. It isn’t. It’s an infrastructure, security, and compliance project with physical logistics attached.
Beyond Boxes and Bubble Wrap The IT Director’s Relocation Reality
Most office relocation services market speed, packing, and furniture setup. Those matter, but they don’t address the risk that keeps IT leadership up at night: active systems going offline, storage media falling out of chain of custody, and legacy assets getting discarded without documented destruction.
That pressure is showing up in the market. From March 2022 to March 2023, 9% of publicly traded American corporations shifted their headquarters, the highest rate in seven years, according to Camoin Associates’ summary of relocation trends. More moves mean more compressed timelines, more site consolidations, and more aging equipment that won’t make the trip.

What general move planning misses
A facilities-led checklist usually covers loading docks, signage, desks, and conference rooms. It rarely answers questions like these:
- Asset accountability: Which laptops, switches, servers, UPS units, and storage arrays are moving, retiring, or held in staging?
- Data exposure: Which devices contain regulated data, cached credentials, local backups, or archived records?
- Dependency mapping: Which applications fail if a single firewall, IDF switch, or storage shelf comes up late?
- Liability transfer: Who signs for every serialized asset, and who issues destruction documentation for what gets retired?
A furniture planner can optimize square footage. For workspace flow, even resources like furniture insights for Albany area homeowners can spark ideas about making smaller footprints work. But IT still has to solve a different problem: how to move the company’s digital nervous system without losing control of hardware, data, or uptime.
Practical rule: If your office relocation services partner can’t talk confidently about chain of custody, data-bearing media, and de-install sequencing, they’re only solving half the move.
Teams handling complex transitions usually need a partner that understands both logistics and technology. A good reference point is specialized office relocation support for IT-heavy moves, where relocation is treated as controlled asset movement, not just transportation.
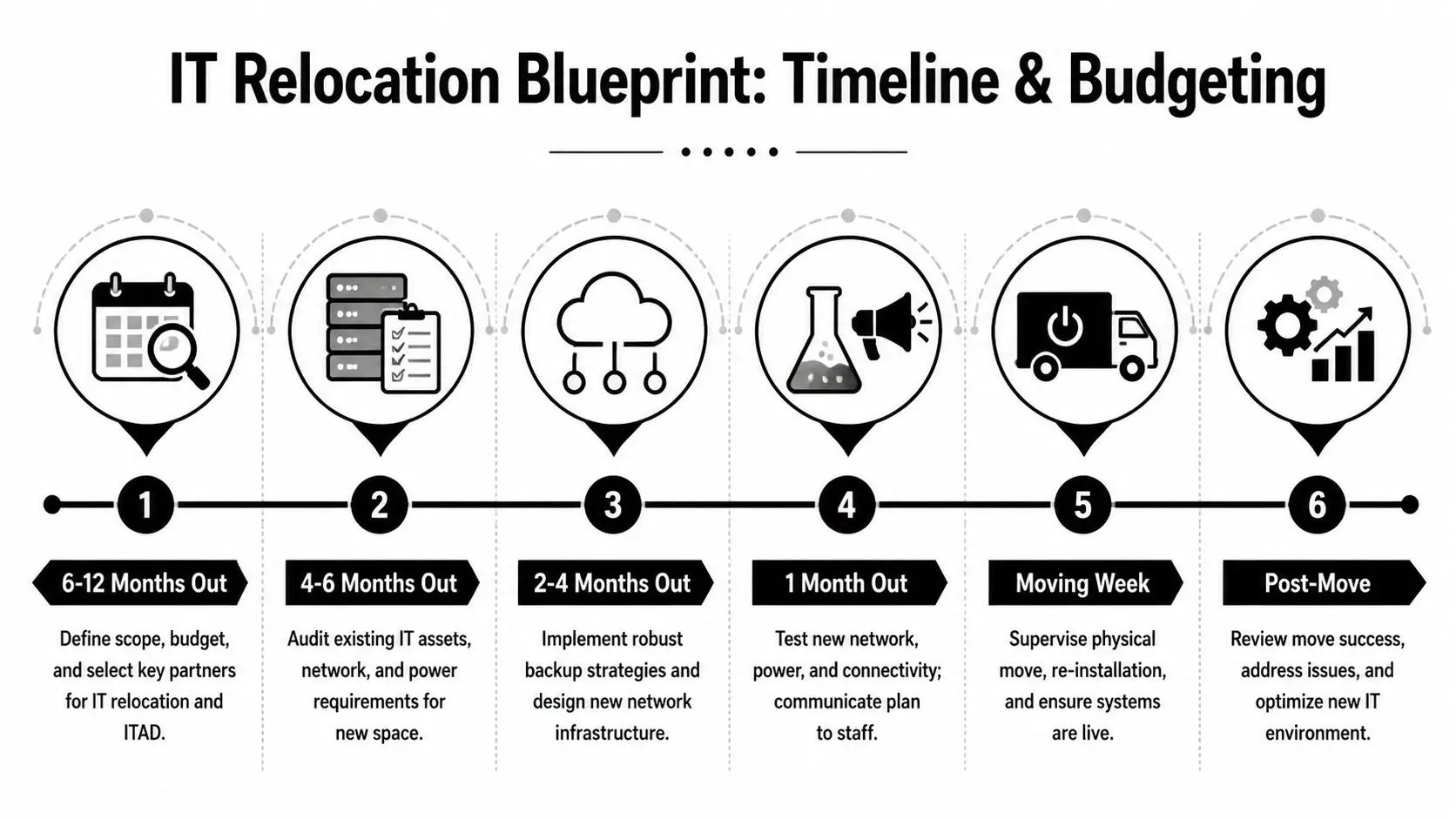
The Strategic Relocation Blueprint Timeline and Budgeting
Office moves go sideways early, not late. The failure point is usually the planning window, when leadership approves a target date before anyone has priced de-install labor, cutover testing, secure destruction, temporary storage, or after-hours access.
According to Interaction’s office relocation checklist, office relocations typically require 6-12 months of detailed planning. That time disappears fast once lease dates, construction punch lists, and carrier schedules enter the picture.
Start with scope before budget
Don’t build the budget from the mover’s quote. Build it from the environment you have.
Create four categories:
Production infrastructure
Servers, storage, core networking, telecom gear, conference room systems, badge systems, and specialty equipment.End-user environment
Laptops, docks, monitors, printers, spare inventory, loaner pools, and remote worker kits stored onsite.Retired or surplus assets
Old desktops, failed drives, obsolete network gear, and anything leadership doesn’t want to pay to move.Site-readiness dependencies
Power, cooling, rack layouts, carrier handoff, ISP turn-up, MDF and IDF readiness, and access control.
If you skip this step, your budget becomes fiction. The most expensive equipment isn’t always the hardest to move. Often it’s the equipment with the most dependency risk or the highest compliance burden.
Budget the line items people forget
IT-specific relocation costs are often underestimated at the start, which is one reason projects overrun. In practice, the missed items are predictable:
- De-install labor: Careful shutdown, labeling, unracking, and packaging takes longer than people expect.
- Staging and storage: Sometimes gear must leave the old space before the new room is fully ready.
- Secure destruction: Drives, backup media, and failed devices need documented destruction, not informal disposal.
- Re-cabling and cleanup: Moves expose years of bad patching habits and undocumented circuits.
- Testing time: User acceptance, print queues, Wi-Fi behavior, badge access, and room systems all need validation.
- Compliance support: Regulated organizations often need extra review around media handling and documentation.
A good planning reference outside the IT lens is Blu Monaco's office planning guide, especially for thinking through how headcount, layout, and space usage affect what IT must support on day one.
Build a timeline that reflects technical reality
I’ve had the best outcomes when the move calendar is built around decision gates, not just dates on a project board.
| Planning window | What must be decided |
|---|---|
| 6-12 months out | Scope, budget ownership, relocation lead, ITAD partner, building constraints |
| 4-6 months out | Asset audit, carrier planning, rack layouts, power and network design |
| 2-4 months out | Backup validation, retirement list, staging plan, destruction workflow |
| 1 month out | Move runbook, staff communications, escalation tree, cutover rehearsal |
| Move week | Final backup checks, de-install, transport, install sequencing, go-live support |
| Post-move | Asset reconciliation, destruction certificates, issue log, optimization |
The strongest relocation plans make three decisions early: what must stay live, what can tolerate downtime, and what should never be moved at all.
Form a relocation committee that can actually decide things
Too many committees are informational only. For a move to work, the group needs decision-makers from IT, facilities, security, finance, and business operations.
Keep the group small. Assign one owner for each of these questions:
- Who approves disposal versus relocation
- Who signs off on data destruction requirements
- Who owns vendor coordination
- Who has authority to delay the move if the new site isn’t ready
For organizations moving across multiple sites or consolidating departments, a nationwide office relocation partner for business IT projects can simplify scheduling, logistics coordination, and surplus asset handling under a single operating model.
Assembling Your A-Team Vetting Relocation and ITAD Vendors
A general mover can transport desks and boxed monitors. That doesn’t make them qualified to handle domain controllers, SAN shelves, firewall pairs, or pallets of retired laptops with intact storage.
That distinction matters because the vendor choice determines whether your move is merely inconvenient or materially risky.

What a qualified partner should be able to answer
Ask direct questions. Vague answers are disqualifying.
- Chain of custody: How do you document possession changes from rack removal through final delivery or destruction?
- Data destruction method: Do you support wiping, degaussing, shredding, or a combination based on device type and policy?
- Asset tracking: Can you track serialized assets individually, not just by pallet or room?
- Insurance and incident handling: What happens if a data-bearing asset is lost, damaged, or unaccounted for in transit?
- Technician capability: Who is doing the de-rack and re-rack work, movers or trained IT technicians?
- Documentation: Do you provide certificates of destruction and recycling records tied to specific assets?
General mover versus ITAD specialist
The easiest way to evaluate office relocation services is to separate transport capability from data risk capability.
| Vendor type | Usually handles well | Usually misses |
|---|---|---|
| General commercial mover | Furniture, cartons, basic office equipment, floor-by-floor coordination | Media sanitization, serialized audit trail, compliance documentation |
| IT relocation specialist | Rack equipment, structured de-install, staged transport, technical reinstall | May not manage end-of-life disposition deeply |
| Certified ITAD partner | Data destruction, downstream accountability, liability transfer, recycling records | May need coordination with relocation crew for active production systems |
The best outcomes usually come from a coordinated model where relocation and ITAD functions are planned together. When those scopes are split without a shared runbook, retired assets tend to pile up in closets, loading docks, and temp rooms. That’s exactly where accountability gets weak.
Vendor evaluation gets easier when you ask for process evidence, not promises.
A practical starting point is a vendor due diligence checklist for ITAD and relocation review. It helps separate polished sales language from operational maturity.
Warning signs during procurement
Watch for these patterns:
- One-price-fits-all quotes: Serious vendors need detail about asset counts, media types, access windows, and site conditions.
- No discussion of retired equipment: If they only talk about what’s moving, they’re ignoring where much of the risk sits.
- No mention of certificates: Without destruction and recycling documentation, you’ll struggle in an audit.
- Reliance on verbal assurances: If chain of custody isn’t documented, it didn’t happen in a defensible way.
Executing the IT Migration From De-Installation to Go-Live
Execution is where planning becomes visible. Good teams make it look calm because the hard decisions were already made. Bad teams improvise under pressure, and that’s when ports get mislabeled, firmware mismatches surface, and business units discover that “the network is up” doesn’t mean their applications work.
According to enterprise relocation benchmarks summarized by DataIT, expert IT relocation methodologies can reduce total migration time by 40-50% compared to in-house efforts and achieve 98-99% success rates in minimizing downtime.
Phase 1 Audit what actually exists
Start with a full inventory, not the spreadsheet someone updated last year. Use your CMDB, endpoint management platform, barcode records, and rack elevations to reconcile what is physically present.
For active environments, label:
- Business-critical gear that must return to service first
- Supporting infrastructure such as switches, PDUs, console devices, and UPS hardware
- User-facing assets assigned to departments, executives, and conference rooms
- Retire-in-place assets that should be diverted to destruction or recycling
If you use ServiceNow or another CMDB, lock the asset list before move week and only allow controlled updates. Loose inventory discipline turns a manageable cutover into a scavenger hunt.
Phase 2 Build rollback and failover into the move
A relocation plan without contingency planning is just optimism. Validate backups. Confirm failover order. Make sure application owners know their recovery sequence and who signs off when systems are ready for users.
The benchmark methodology cited above includes risk assessment, bandwidth modeling for migration, and failover simulation. In practice, that means testing dependencies before trucks are loaded, not after.
A clean move window starts with one uncomfortable meeting: force every application owner to say what breaks if their system comes up late.
Phase 3 Control packing and transport like a security event
IT equipment shouldn’t be packed like office décor. Anti-static materials, secure crates, and documented loading order matter because the loading sequence often becomes the install sequence.
For sensitive moves, require:
- Serialized check-out and check-in
- Tamper-evident labeling where appropriate
- Separate handling for data-bearing assets
- Chain-of-custody logs tied to responsible personnel
- Clear segregation between move assets and disposal assets
This is also where teams get burned by mixing retired devices with production equipment. Once both categories share staging space without controls, accountability gets muddy fast.
Phase 4 Reinstall in dependency order
Don’t rack equipment in the order it arrives. Rack it in the order the environment needs to come alive.
A practical sequence often looks like this:
Power and environmental checks
Confirm circuits, cooling, rack placement, and physical security before anything is mounted.Core network and internet handoff
Firewalls, switching core, WAN edge, and DNS-dependent services should be restored first.Authentication and management systems
Directory services, remote management, monitoring, and logging come next.Storage and compute layers
Hypervisors, SAN or NAS connectivity, and workload hosts follow.Departmental and user-facing systems
Printing, room systems, local file shares, and endpoint deployment stations can come after the backbone is stable.
Phase 5 Test beyond basic connectivity
A link light proves almost nothing. Test the things users will notice.
| Test area | What to verify |
|---|---|
| Identity | Logins, MFA prompts, group policy, SSO behavior |
| Network | VLAN assignment, Wi-Fi roaming, DHCP, DNS resolution |
| Applications | Core line-of-business access, latency, printing, file shares |
| Security | Camera systems, badge access, monitoring alerts, endpoint health |
| Recovery | Backups running, replication status, restore workflow still valid |
A structured office relocation execution plan for IT environments helps keep these phases aligned so transport, reinstall, and surplus handling don’t compete for the same staff at the same time.
What doesn’t work
Some patterns fail almost every time:
- Last-minute labeling
- Assuming the new site is ready because construction says it is
- Treating conference room tech as nonessential until executives need it
- Letting business units self-move devices
- Waiting until post-move to decide what to do with retired hardware
Managing Digital Ghosts Secure Data Destruction and Asset Disposition
Every office move creates a second project that many teams underestimate: what to do with the equipment that should not enter the new space. That includes obsolete servers, failed hard drives, storage arrays at end of life, aging laptops, old networking gear, and miscellaneous devices sitting in closets because no one wanted to own the decision.
This is the part most relocation guides barely touch, and it’s where the biggest preventable exposure often lives.
According to Dependable Movers SF’s discussion of office relocation services and ITAD gaps, 68% of business data breaches in 2025 were traced back to improper disposal of old hardware. The same source notes that regulations like the FTC Disposal Rule mandate secure destruction, with non-compliance fines averaging $4.5M.

Why wiping alone isn’t always enough
A policy that says “we wipe drives before disposal” sounds responsible until you test how it works in the field. Drives fail. Devices arrive without power supplies. Storage media may be encrypted, damaged, or no longer supported by your standard workflow. Some assets never make it to the bench because they get mixed into move debris or sit in a cage waiting for “later.”
That’s why disposition needs a formal method selection process:
- Data wiping works when the media is functional, the asset has reuse value, and the process is documented.
- Degaussing may fit specific magnetic media destruction workflows where reuse is not the goal.
- Physical shredding is the clearest option for failed drives, high-risk data, or policies that require irreversible destruction.
The document that matters most
The most important deliverable in this phase isn’t the truck manifest. It’s the serialized Certificate of Data Destruction.
That document should tie individual assets or media to the destruction event and show that custody passed to a qualified downstream process. Without it, legal and compliance teams are left with assumptions instead of evidence.
If your relocation closes with a cleaned-out server room but no destruction certificates, the risk didn’t disappear. It just became harder to prove.
Build a disposition stream separate from the move stream
Don’t let retirement decisions happen ad hoc on move day. Create a dedicated disposition workflow before de-install begins.
A workable model includes:
- A retirement list approved by IT, security, and finance
- A red-tag or similar visual marker for assets that must not go to the new site
- Separate staging zones for relocation, storage, and destruction
- Named custody owners at each handoff
- Final reconciliation against destruction certificates and recycling records
This is also the right time to evaluate buyback potential. Some equipment can return value when it’s still functional and marketable, but that only works if the asset is identified early, sanitized correctly, and kept out of the scrap stream.
For organizations handling storage media during a move, secure hard drive destruction services with documented custody are a critical control, not an optional cleanup task.
Compliance is an operational practice
The FTC Disposal Rule gets attention because it’s concrete, but the broader lesson applies across regulated sectors. Healthcare, finance, government, and education all need a disposal process that someone can audit later. That means records, custody, method selection, and proof.
The relocation is temporary. The compliance record lasts much longer.
The Final Checkpoint Post-Move Verification and Optimization
A move isn’t complete when users can log in. It’s complete when every asset is accounted for, every retired device is documented, and the new environment performs the way it was designed to.
Reconcile the inventory
Start with the pre-move audit and match it against what arrived, what was installed, what remains in storage, and what entered destruction. Don’t settle for room-level confirmation. Reconcile to the asset level wherever possible.
Use four buckets:
- Installed and operational
- Received but not yet deployed
- Transferred to certified disposition
- Exception items requiring investigation
If an item doesn’t fit one bucket, treat it as an incident until resolved.
Validate the environment users actually experience
The post-move test shouldn’t be limited to infrastructure metrics. Walk the building and test workflows from the user side.
Check:
- Conference rooms: displays, conferencing platforms, microphones, and room schedulers
- Department printers and scanners: especially for finance, legal, and records teams
- Wi-Fi in real use areas: offices, huddle rooms, break areas, and reception
- Badge access and cameras: confirm both security and logging visibility
- Remote access: VPN or equivalent access for hybrid staff after the move
The fastest way to lose confidence after a successful cutover is to ignore the “small” systems executives and front-line teams use all day.
Close the documentation loop
By the end of the project, your file should contain:
| Required record | Why it matters |
|---|---|
| Final asset reconciliation | Confirms nothing disappeared between sites |
| Chain-of-custody records | Shows who handled data-bearing assets |
| Certificates of destruction | Proves retired media was destroyed properly |
| Recycling documentation | Supports environmental reporting and downstream accountability |
| Issue log and remediation notes | Helps with audit defense and future moves |
Optimize after stability returns
Once the environment is stable, use the move as a cleanup opportunity. Retire duplicate circuits, update diagrams, fix legacy labeling, and tighten storage practices for spares and returned equipment.
Good office relocation services get you into the new space. Strong IT governance makes the new space better than the old one.
Secure Your Move from Start to Finish
The safest office relocations treat IT as the center of the project, not the department that reconnects things after the trucks leave. Planning, vendor vetting, migration control, and certified asset disposition all belong in the same operating plan.
A productive workplace also depends on what happens around the technology. For teams thinking about handoff readiness after construction and move-in, this guide to a productive office environment is a useful companion resource because it addresses the condition of the space employees return to.
If you’re moving an office, consolidating locations, or closing a site, don’t leave retired hardware and data-bearing media for the final week. Handle disposition early, document every handoff, and require proof of destruction before the project closes.
Contact Beyond Surplus for certified office relocation services, secure IT asset disposal, and compliant data destruction that protects your organization from pickup through final documentation.