If you're managing IT in Dallas, there's a good chance you have a back room, cage, or storage closet full of retired laptops, dead switches, aging servers, and monitors nobody wants to touch. The equipment is no longer in production, but it still carries risk. In practice, e recycle starts long before a truck shows up.
For business teams, this isn't a housekeeping issue. It's a security, compliance, and asset recovery decision. A proper e recycle workflow accounts for inventory control, data destruction, transport, downstream handling, and final reporting. Anything less leaves gaps you may have to explain later.
The Hidden Risks of Your Retired IT Equipment
A pile of retired hardware looks harmless until someone asks what's on it, who approved its removal, and where it went. Old desktops, SAN shelves, backup appliances, and employee laptops often sit untouched because no one wants to disrupt operations or own the disposal process. That delay creates exposure.

What the closet is really holding
Some devices still contain regulated data. Others contain components that require controlled downstream processing. Many also retain resale value that disappears as equipment ages, firmware support ends, and cosmetic condition worsens.
The global backdrop makes the business case clear. The world generated 62 million metric tonnes of e-waste in 2022, an 82% increase from 2010, and only 22.3% was formally recycled. That stream contained an estimated US$62 billion in recoverable resources, according to Global e-waste figures summarized here.
The three risks that matter most
- Data exposure. Retired hard drives, SSDs, phones, and copiers can still hold customer records, financial files, credentials, and internal documents.
- Compliance failure. If disposal isn't documented, you may struggle to show that assets were handled under your internal policy and external requirements.
- Lost recovery value. Equipment that could have been redeployed, remarketed, or harvested for parts often sits until it's worth less.
Old equipment isn't low risk because it's powered off. It's high risk because nobody is watching it.
That is why companies move from ad hoc disposal to a documented business e-waste recycling process. The goal isn't just to clear space. The goal is to close liability.
Preparing Assets for Secure E-Recycle Pickup
Before pickup, your internal controls matter more than the truck schedule. If inventory is sloppy at the start, every later document is weaker.

Start with an asset-level inventory
Build a list that includes device type, manufacturer, model, serial number, asset tag, location, and assigned department. If a device stores data, flag that clearly. If it's leased, note that too.
A workable pickup file usually includes:
- User devices such as laptops, desktops, tablets, and phones
- Infrastructure gear including servers, storage, firewalls, and switches
- Peripherals like docks, monitors, printers, and badge readers
- Loose media such as hard drives, backup tapes, and SSDs
Separate by handling path
Not every device should follow the same route. Sort assets into practical groups:
Reuse or remarket candidates
Newer laptops, servers, and networking gear may justify testing and data wiping.Destroy on sight media
Failed drives, highly sensitive storage, and damaged media often belong in the shredding stream.Commodity recycling
Broken monitors, obsolete accessories, and low-value scrap can be staged for standard recycling.
Tag and stage assets properly
Use your existing asset tags if they're readable. If not, apply temporary project labels before anything moves. Keep high-sensitivity items in a separate secured area. Don't mix boxed laptops for buyback with loose drives intended for destruction.
Practical rule: If a device can't be matched to a line item, treat it as an exception before pickup day, not after.
A clean staging area also speeds handoff. Palletize where it makes sense. Keep cords, power supplies, and rails with hardware that may be remarketed. For scrap-only material, consolidation is usually enough.
Assign one owner for the project
Facilities may control dock access. Procurement may own lease returns. Security may control badging. IT should still assign one person to reconcile the manifest.
That person should confirm:
- Counts match the pickup list
- Sensitive media is isolated
- Access paths are ready for carts, pallets, or liftgate service
- Internal approvals are captured before release
Good e recycle programs don't start at the processor. They start inside your building with control over every serial number you plan to release.
Data Destruction Wiping vs Shredding
Every business disposal project hits the same decision point. Should you preserve the asset and wipe the data, or destroy the media physically? The right answer depends on risk tolerance, device condition, and whether asset recovery matters.

Secure ITAD methodology requires either data sanitization using standards like DoD 5220.22-M with 3-pass overwrite or physical shredding to NSA/CSS specifications with particle size under 2mm. Certified processors improve success rates by 30-50%, while uncertified recyclers have been found to resell assets instead, as outlined in this secure ITAD guidance.
When wiping makes sense
Wiping is usually the better option when the device still has market value and the media is functioning normally. That's common with recent business laptops, desktops, and some server drives.
Wiping works best when you need:
- Asset recovery through resale or redeployment
- Certified erasure records tied to serial numbers
- Less material destruction for sustainability goals
When shredding is the better call
Shredding is the safer choice when media is failed, encrypted status is unknown, chain of possession was weak, or the data profile is highly sensitive. Healthcare, finance, legal, and government teams often default to physical destruction for those reasons.
Use shredding when:
- Drives are damaged and can't be wiped reliably
- Policy requires physical destruction
- Residual value is low and certainty matters more than reuse
You can review a typical hard drive shredding workflow for business media before choosing your destruction path.
Data Wiping vs. Physical Shredding A Comparison for Businesses
| Factor | Data Wiping (NIST 800-88) | Physical Shredding |
|---|---|---|
| Primary outcome | Sanitizes data while preserving hardware | Destroys media irreversibly |
| Best fit | Reusable laptops, desktops, functioning drives | Failed drives, highly sensitive media, end-of-life storage |
| Value recovery | Supports resale and redeployment | Eliminates resale of the media itself |
| Documentation | Erasure reporting tied to the asset | Destruction reporting tied to the media |
| Security posture | Strong when process is validated | Highest certainty when destruction is required |
| Sustainability trade-off | Extends useful life of equipment | Prioritizes final destruction over reuse |
If the business objective is maximum resale, wipe. If the business objective is maximum certainty, shred.
A mature e recycle program often uses both methods in the same project. That isn't inconsistency. It's good control.
Ensuring Compliance with Chain of Custody
The handoff is where many companies lose visibility. A vendor can say the material was processed properly, but if you can't trace what left your site and how it was handled, you still hold the risk.
Documentation is the control
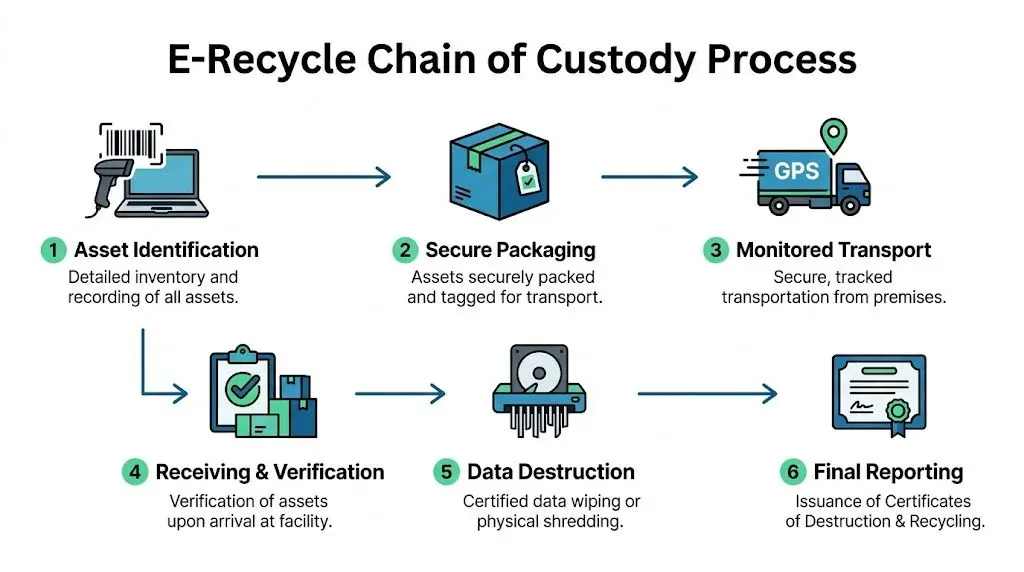
Chain of custody isn't filler paperwork. It's the record that links internal inventory, pickup manifest, receiving verification, processing method, and final certificate.
Certified recycling processes such as R2v3 mandate strict chain-of-custody tracking and can boost material recovery success by 40% compared to non-certified operations. Unverified facilities also face contamination and illegal export problems that don't transfer liability away from the original owner, according to this review of e-waste processing pitfalls.
What audit-proof reporting should include
Look for reporting that identifies individual assets or clearly grouped media and ties them to a final disposition. At minimum, your file should show:
- Pickup record with date, site, and shipment reference
- Receiving confirmation from the processing facility
- Serialized destruction or erasure detail where applicable
- Final certificate set for destruction and recycling
A business that needs evidence for auditors or legal review shouldn't accept vague summary language.
Certificates are not just receipts
A certificate matters because it proves what happened after release. If your processor issues a generic one-page statement with no identifying detail, it won't help much in an investigation.
For destroyed media, ask for a formal certificate of hard drive destruction tied to the shipment or serial record. For recycled equipment, keep the recycling certificate with the same project file.
The safest assumption is simple. If you can't document the path, you can't prove compliant disposal.
Many e recycle programs separate into two groups. One group clears space. The other closes liability with records that survive an audit, customer questionnaire, or incident review.
Coordinating E-Recycle Logistics for Your Business
Once the project scope is clear, logistics should feel routine. If the vendor makes pickup hard, your internal team delays the job.

The U.S. electronic goods recycling industry is projected to reach $28.1 billion by the end of 2024, and only 25 states have e-waste laws, which is why enterprises benefit from a consistent multi-site service model across locations, as summarized by industry data on U.S. electronic goods recycling.
What a smooth pickup process looks like
The vendor should ask for practical information early:
- Site profile such as office, warehouse, clinic, school, or data center
- Material mix including pallets, loose equipment, and sensitive media
- Access details like dock availability, elevators, COI requirements, and pickup windows
Good planning avoids day-of surprises. That's especially true for decommissions, after-hours pickups, and multi-floor removals.
Multi-site coordination matters
Dallas companies rarely retire equipment from one room at one address. They may have branch offices in Texas, remote staff returns, and colocated gear elsewhere. A unified process is easier to manage than different local arrangements in each market.
For teams comparing operating models, these e-recycle logistics insights are useful because they frame transport and handling as part of the control system, not just trucking. That's the right way to look at it.
Beyond Surplus provides business e-waste pickup coordination for organizations that need scheduled collection, secure transport, and project-based removals across locations.
What your staff should and shouldn't do
Your team should verify counts, release only approved assets, and document exceptions. Your team shouldn't be improvising packaging standards, arguing over final downstream handling, or guessing which devices require destruction.
When logistics are set up correctly, pickup day is uneventful. That's what you want.
Maximizing Value with IT Asset Disposition
Disposal doesn't always mean pure cost. The better question is which assets still deserve testing, wiping, and resale before they enter the recycling stream.
Where recovery value usually exists
Recent business laptops often retain the strongest remarketing potential, especially when they have intact screens, chargers, and consistent specs. Servers, network gear, and some enterprise components can also produce meaningful returns if they're complete and still in demand.
Globally, businesses miss out on an estimated $91 billion in recoverable materials from e-waste annually. Through professional ITAD services, laptops can fetch $50-300, and servers can be worth thousands, according to this discussion of e-waste value recovery.
What separates real recovery from wishful thinking
Value depends on condition, age, configuration, testing results, and resale channel. A stack of mixed, untested laptops with missing power supplies is harder to monetize than a clean batch with known specs and wipe-ready drives.
For that reason, strong ITAD programs usually:
- Test and grade devices before pricing
- Separate resale candidates from scrap early
- Tie erasure records to assets destined for remarketing
- Report returns clearly instead of burying them in disposal invoices
If your business wants to offset project costs, review how IT asset recovery services for business equipment handle testing, resale pathways, and settlement reporting. Good e recycle work doesn't force you to choose between compliance and value. It uses the right path for each asset.
If your Dallas team needs a documented process for business e recycle, data destruction, pickup logistics, and IT asset recovery, contact Beyond Surplus.