When a federal office closes fast, the riskiest work doesn’t happen in the boardroom. It happens in hallways, storage rooms, server closets, loading docks, and spreadsheets that stop matching reality the moment people start moving devices. That’s why a usaid office cleanout should be treated as a controlled decommissioning program, not a facilities chore.
The 2025 USAID shutdown made that obvious. According to the USAID Office of Inspector General’s Top Management Challenges for Fiscal Year 2025 report, over 10,000 employees were required to return IT equipment including laptops, tablets, cellphones, and other electronics, while staff were barred from offices and the agency moved through a broader dismantling. In that environment, every missing laptop becomes a security event, every undocumented pickup becomes an audit problem, and every informal decision can follow a program manager for years.
Navigating an Unprecedented Government Office Cleanout
A government shutdown cleanout fails when leaders assume the work is mostly about hauling away equipment. It isn’t. Instead, the job is controlling custody, documenting decisions, and preventing unmanaged data exposure while operations are being wound down under pressure.

The USAID case shows the scale. The OIG report documents a cleanout involving over 10,000 employees returning devices and other government property during a period when access was already restricted and programs were being dismantled. For any IT director or compliance lead, that changes the playbook immediately. You need asset control before pickup, data destruction before disposition, and signed records before anyone declares the project complete.
What works in the first seventy two hours
The first move is to freeze improvisation. Don’t let local offices create their own disposal rules. Don’t allow staff to leave equipment in reception areas. Don’t mix redeployable assets with destruction candidates.
Use three lanes from day one:
- Return lane for assigned user devices and accessories
- Infrastructure lane for servers, storage, networking, and shared hardware
- Exception lane for damaged, untagged, locked, or high-sensitivity assets
That structure sounds simple, but it prevents most of the mess that later shows up in audit files.
Practical rule: If a device can’t be matched to an owner, serial record, or custody event, treat it as high risk until proven otherwise.
The four pillars that keep the project defensible
A serious usaid office cleanout stands on four controls:
Strategic planning
Someone must own scope, approvals, and escalation paths.Secure logistics
Equipment movement needs custody controls, not just trucks.Certified data destruction
You can recycle metal and plastic later. You can’t undo a data leak.Compliant documentation
If the paperwork is weak, the project is weak.
Government teams that need a service framework for public-sector electronics disposition usually start by reviewing providers built for government electronics recycling in Georgia, then adapting the process for their own footprint and agency rules.
Phase One Strategic Planning and Stakeholder Alignment
The project starts before anyone touches a device. If leadership skips governance, the rest of the cleanout turns into a series of disconnected pickups, conflicting instructions, and approval gaps.
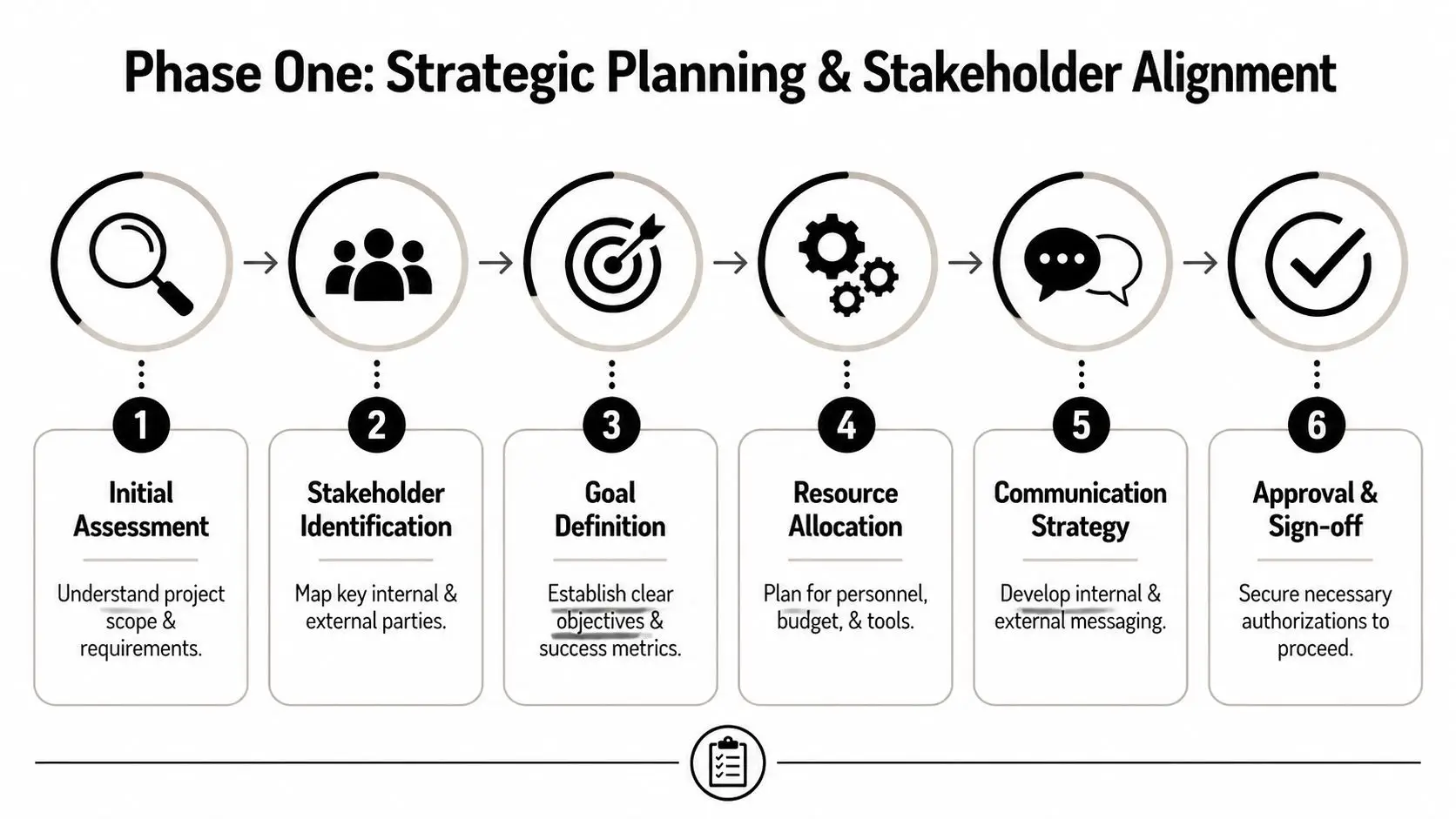
Build the command group first
A workable shutdown team usually includes IT, information security, facilities, legal, procurement, records management, finance, and site security. In a government closure, HR and program leadership also need seats at the table because employee separation activity often overlaps with equipment return deadlines.
Each group needs a defined decision right. Legal decides acceptable documentation standards. IT decides handling methods for different asset classes. Facilities controls access windows. Finance reconciles property and write-off questions. Procurement manages vendor terms. If those lines blur, delays multiply.
Put the project charter in writing
A charter doesn’t need to be long. It does need to answer the questions people will otherwise argue about on pickup day.
Include these points:
Scope boundaries
Name which offices, storage areas, data rooms, and leased spaces are in scope.Asset categories
Separate user endpoints, infrastructure, peripherals, telecom gear, and specialty electronics.Authority chain
Identify who can approve destruction, resale, transfer, or hold orders.Security rules
Define packaging, storage, escort requirements, and documentation thresholds.Exit criteria
State what must exist before a site is considered closed.
Map the sites like an operations planner
Large cleanouts don’t fail because leaders forgot a headline task. They fail because no one mapped the side rooms, loaner closets, remote cabinets, project labs, and after-hours storage cages. A proper site map should include access constraints, elevator reservations, dock rules, and any location where orphaned electronics tend to accumulate.
A simple site matrix helps.
| Location type | Typical risk | Required control |
|---|---|---|
| Office floors | Missing user devices | Assigned return roster |
| Server rooms | High data exposure | Controlled removal window |
| Storage rooms | Unrecorded surplus | Wall-to-wall inventory |
| Remote offices | Inconsistent handling | Standardized local kit |
Shutdowns expose weak ownership fast. The device nobody claimed during normal operations becomes the device everyone argues about during decommissioning.
Secure signoff before execution
Waiting until assets are stacked on pallets to request approval is one of the worst mistakes a manager can make. Get signoff on handling methods, approved vendors, and reporting format before execution begins. That protects the team when a stakeholder later asks why an asset was shredded instead of wiped, or sold instead of redeployed.
Good planning feels slower at the start. It isn’t slower. It removes rework, shortens exception handling, and keeps the cleanout from becoming a public records and security problem.
Phase Two Asset Inventory and Secure Logistics
Inventory work is where cleanouts become real. This is the point where assumptions meet serial numbers, and where undocumented surplus starts showing up in places no asset register captured.

Run a wall to wall inventory, not a spreadsheet reconciliation
A cleanout team should never rely only on the existing CMDB or procurement records. Those systems help, but shutdown conditions expose every exception: swapped laptops, retired printers still sitting in closets, loaner phones, failed drives in desk drawers, and lab devices that were never booked correctly.
Use a floor-based method:
- Sweep each area physically and log every asset found
- Scan or record serial numbers at the point of discovery
- Apply status labels such as redeploy, wipe, shred, hold, or recycle
- Photograph unusual assets that may need later validation
- Quarantine exceptions in a secured holding area
This is also where operational discipline from preventive IT maintenance pays off. Teams that maintained current device records and lifecycle habits before shutdown usually face fewer custody disputes and fewer mystery assets during cleanout.
Classify before you move
Not all electronics belong on the same cart. A retired monitor doesn’t carry the same risk as a laptop from a health program, and neither should travel under the same assumptions.
A practical field classification model looks like this:
Category A high sensitivity
Laptops, desktops, servers, storage arrays, removable media, mobile devices, and any system that may store regulated or mission data.
Handling rule: sealed containers, logged custody, secured staging, priority destruction decision.
Category B infrastructure support
Switches, routers, UPS components, VoIP hardware, rack accessories, KVM gear, and related hardware.
Handling rule: serialized removal, rack position verification where relevant, matched transport manifests.
Category C low sensitivity electronics
Displays, docks, keyboards, mice, cabling, and non-data peripherals.
Handling rule: bulk packed by type after confirming no embedded storage risk.
Vet the logistics partner like an auditor would
The wrong transportation setup ruins a good inventory. Secure logistics for a usaid office cleanout means scheduled pickups, custody signatures at transfer points, tamper-aware packaging, documented arrival, and a processing workflow that matches what was promised in the statement of work.
When reviewing an ITAD provider, ask for:
- Chain-of-custody process from site release to final processing
- Data destruction options including on-site and off-site methods
- Exception handling for damaged or unidentified devices
- Documentation samples for manifests and certificates
- Pickup capability across all required U.S. locations
Organizations evaluating removal support for larger shutdowns often compare providers that handle IT asset removal services across multiple facilities and equipment types.
If the vendor can’t explain what happens between your loading dock and their processing floor, you don’t have secure logistics. You have hope.
Stage the move so sites don’t collapse into confusion
Don’t empty an office in one undifferentiated push. Sequence the work. Start with storage and surplus areas, then user-return zones, then shared equipment, then server and telecom spaces. That order reduces disruption and shrinks the volume of unmanaged items still in circulation.
The best-run projects also establish a same-day reconciliation routine. Inventory collected, inventory loaded, and inventory received should be compared continuously. Problems found on day one are manageable. Problems found after the last truck leaves are expensive.
The Critical Path Data Destruction and Chain of Custody
In a government shutdown, data handling is the project. Trucks, pallets, and recycling containers are secondary. If sensitive information escapes through a decommissioned laptop or storage device, no amount of recycling paperwork will rescue the team that approved the process.

The stakes were unusually high in the USAID case. Harvard T.H. Chan School of Public Health summarized that USAID’s two-decade legacy saved an estimated 92 million lives, and the 2025 shutdown involved the liquidation of assets tied to global health programs. That same review terminated over 5,300 awards, including 86% of maternal and child health programs, underscoring how sensitive information on decommissioned federal electronics can be in this kind of event, as described in Harvard’s coverage of the USAID shutdown and resulting deaths.
Choose the destruction method by risk, not convenience
Three methods usually come up.
Data wiping works when media is functional, the device is approved for sanitization, and you need a documented overwrite process.
Degaussing may fit some magnetic media, but it isn’t a universal answer and often changes downstream asset value.
Physical destruction is the safer choice for failed drives, unknown media, and high-sensitivity devices where certainty matters more than resale.
The mistake is treating all three as interchangeable. They aren’t. Pick the method based on media type, data sensitivity, and whether the organization can defend that choice later.
NIST alignment and custody records matter more than marketing language
Vendors love broad phrases like secure recycling and compliant disposal. Those terms aren’t enough. The team needs method-level documentation and a custody trail that shows who possessed each asset, when it moved, where it went, and what final destruction action occurred.
For organizations that need a benchmark for sanitization decisions, the practical reference point is NIST SP 800-88 guidance. What matters operationally is that the chosen method matches the media and that the record set can survive an audit or investigation.
What a defensible chain of custody includes
A usable chain-of-custody record should document:
- Asset identifiers such as serial number or internal tag
- Transfer events with date, time, location, and signatures
- Container controls including seal or pallet references where used
- Processing outcome such as wipe, shred, hold, recycle, or resale
- Exception notes for damaged, unreadable, or untagged items
Weak custody records usually fail in the same way. They describe batches too broadly, omit handoff names, or don’t connect individual assets to destruction outcomes.
Security teams don’t lose sleep over the device that was shredded correctly. They lose sleep over the device that disappeared into a generic pallet count.
The certificate is not a formality
A Certificate of Data Destruction should close the loop between custody and method. If the certificate can’t be tied back to the manifest, it won’t transfer enough practical risk away from the agency. The same is true if the certificate only states that material was processed without identifying what was destroyed or how.
This is where a provider’s process matters. Beyond Surplus offers on-site and off-site hard drive shredding, data wiping, chain-of-custody documentation, and related ITAD support for organizations handling federal-style surpluses. Those are the kinds of controls shutdown teams should require from any vendor under consideration.
Phase Three Compliance Documentation and Value Recovery
Once the last pickup leaves, the most common mistake is assuming the hard part is over. It isn’t. A cleanout isn’t finished until the documentation package is complete, internally reconciled, and usable in an audit, records review, or post-project dispute.
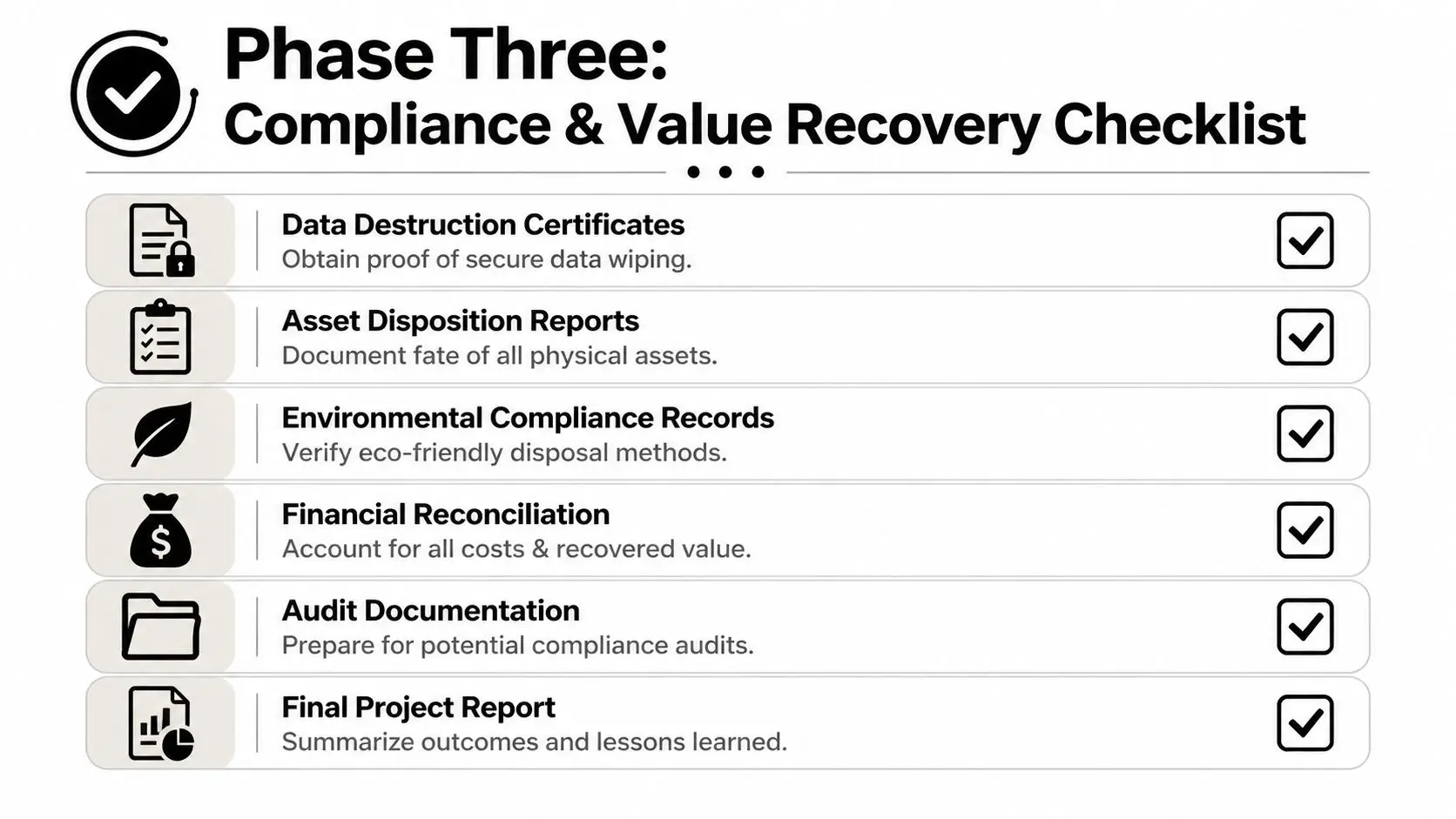
Audit the closeout file before you archive it
The final package should be reviewed like evidence, not like routine admin paperwork. The agency needs to confirm that manifests, custody logs, destruction records, and recycling records agree with one another. If one report says an asset was wiped and another says it was shredded, that conflict has to be resolved before closeout.
A practical review set includes:
- Disposition reports matching original pickup manifests
- Data destruction records tied to specific assets or media lots
- Recycling certificates identifying downstream processing
- Financial reconciliation for any buyback, credits, or service fees
- Exception register showing unresolved or specially handled items
Small administrative habits matter here. Finance and procurement teams that already use disciplined document retention methods, such as the receipt workflows described in how to organize receipts for taxes, usually move through cleanout reconciliation with fewer missing records and less end-of-quarter scrambling.
Know what the certificate actually proves
A certificate transfers practical liability only if it is specific enough to support the chain of events. It should identify the issuing party, service date, asset scope, and method used. It should also align with the manifest numbers and site dates already on file.
For a benchmark, compare your vendor’s format against a documented certificate of destruction process. You’re looking for completeness, not branding.
| Document | What it should answer |
|---|---|
| Manifest | What left the site |
| Chain of custody | Who controlled it in transit |
| Destruction certificate | What data-bearing media was destroyed and how |
| Recycling certificate | What was processed responsibly |
| Financial statement | What value was recovered or charged |
Value recovery is real, but only after compliance
Shutdown teams sometimes chase resale too early. That creates avoidable risk. First decide which assets are eligible for release after sanitization and records checks. Then grade them for reuse, resale, parts harvest, or recycling.
Good recovery programs focus on transparency:
- Clear grading standards for condition and marketability
- Separated reporting for destroyed versus remarketed assets
- Straight reconciliation between gross recovery and service costs
Recovered value can offset project cost, but the bigger win is disciplined closure. When the paperwork, custody record, and financial file all tell the same story, the cleanout is defensible.
Building a Resilient Decommissioning Process
A government office shutdown tests three capabilities at once. It tests planning discipline, execution control, and documentation quality. If one breaks, the others won’t save the project.
The strongest usaid office cleanout programs start with authority and scope. They continue with physical inventory, secure staging, and controlled logistics. They finish with documented data destruction, reconciled certificates, and a closeout package that can stand up to internal review.
That framework works outside government too. Any enterprise decommissioning a regional office, health program, or data-heavy operation faces the same core risks. Missing assets, broken custody, unclear destruction methods, and weak reporting all create downstream exposure.
Teams planning larger site exits or infrastructure retirement usually benefit from reviewing a formal data center decommissioning process before building their own runbook. The principle is the same whether the environment is a branch office or a federal footprint. Control the assets. Control the data. Control the records.
USAID Cleanout Frequently Asked Questions
How should teams handle assets that may contain classified or highly restricted data
Treat them outside the standard commercial ITAD lane unless your internal rules explicitly allow otherwise. Standard wipe-or-shred workflows may not be enough for assets subject to higher handling restrictions. Hold those items in a separate custody stream, confirm agency-specific destruction requirements, and require written authorization before release. The biggest mistake is assuming all federal devices can enter the same processing queue.
What changes when the cleanout spans multiple states or dispersed offices
Central standards matter more than local convenience. Use one manifest format, one asset classification model, one escalation process, and one custody standard across all locations. Let sites adapt to local dock schedules and access constraints, but not to security rules. Cross-state cleanouts usually fail when every office invents its own labeling, storage, and handoff method.
A practical control is to designate one command team that reviews daily exceptions from every site. That prevents local workarounds from turning into permanent record problems.
How can agencies maximize financial return on government property without creating compliance risk
Start by separating eligible remarketing assets from mandatory destruction assets early in the process. Then require sanitization decisions to be documented before any resale path is considered. Recovery improves when equipment is tested, complete, and properly identified, but none of that matters if the release decision can’t be defended.
The wrong approach is to push everything toward resale. The right approach is to preserve recoverable value only where custody, sanitization, and approval records are complete.
If your organization is planning a complex shutdown, office exit, or federal-style device return program, contact Beyond Surplus for secure IT asset disposition, certified data destruction, electronics recycling, and documented logistics support.