When your Atlanta business searches for "secure data destruction near me," you are taking a critical step to shield your enterprise from severe financial and reputational damage. In Georgia, the proper destruction of data on retired hard drives, servers, and corporate laptops is not merely an IT task—it is an essential security protocol for any commercial operation. This guide is for Atlanta-based business owners, IT managers, and procurement professionals seeking to protect their company's sensitive information.
The Business Case for Certified Data Destruction for Atlanta Companies
In today's digital landscape, a single misplaced hard drive can rapidly escalate into a catastrophic liability. Retired IT assets are not just electronic waste; they are repositories of your most sensitive information, from client records and financial data to proprietary trade secrets. A data breach originating from an improperly discarded device can trigger massive regulatory fines, costly legal battles, and a permanent erosion of customer trust.
Just as businesses in Atlanta rely on smart local SEO near me to attract the right customers, you must find the right certified partner to protect your company's most valuable asset: its data.
From Cost Center to Risk Management
It is imperative to reframe the conversation around IT asset disposal. Data destruction is not a simple disposal cost; it is a fundamental component of your risk management strategy. The discussion must evolve from, "How much to get rid of this equipment?" to "How do we protect our company from a data breach?"
This urgency is reflected in the market itself. The secure data destruction industry is experiencing significant growth as businesses grapple with escalating cyber threats and stricter regulations. Projections show the market, valued at approximately $4.4 billion in 2025, is expected to nearly triple to $10.3 billion by 2034.
With global cybercrime costs forecasted to reach a staggering $10.5 trillion annually by 2025, the need for certified destruction that meets standards like the FTC Disposal Rule and HIPAA has never been more critical for Atlanta businesses.
Quick Guide to Finding Secure Data Destruction Services in Atlanta
Finding the right partner involves more than a simple search. You need to vet providers to ensure they meet security, compliance, and logistical requirements for your commercial operations. This table breaks down the essential steps for your business.
| Action Step | Why It's Critical for Your Business | Key Question to Ask Potential Vendors |
|---|---|---|
| Verify Certifications | Ensures the provider follows audited, industry-best practices for security and environmental standards. | "Are you NAID AAA or R2 certified, and can you provide proof for our records?" |
| Review Chain of Custody | Creates an unbroken, documented trail for your IT assets, proving they were securely handled from pickup to destruction. | "What does your chain of custody process look like, and what documentation will our business receive?" |
| Confirm Compliance | Protects your company from legal and financial penalties by ensuring destruction meets regulatory mandates like HIPAA or the FTC Disposal Rule. | "How does your service ensure our business remains compliant with [Your Specific Regulation]?" |
| Get a Certificate of Destruction | Provides the official, legal proof you need to demonstrate due diligence and satisfy auditors. | "Will our company receive a serialized Certificate of Data Destruction for our records?" |
By following these steps, you can confidently choose a provider that not only destroys your data but also protects your business.
Key Benefits of Prioritizing Secure Destruction for Your Enterprise
Investing in a professional data destruction service delivers tangible returns by shielding your organization from multiple threats.
- Mitigates Financial Risk: Prevents costly fines from regulators and helps you avoid the massive expenses tied to breach remediation.
- Protects Brand Reputation: Shows customers, partners, and stakeholders that you take data security seriously, which is essential for building and maintaining trust in the Atlanta market.
- Ensures Legal and Regulatory Compliance: Gives you the documentation you need, like a Certificate of Data Destruction, to prove you've met your legal duties under laws like HIPAA, FACTA, and the FTC Disposal Rule.
Ultimately, partnering with a certified provider like Beyond Surplus ensures your end-of-life IT assets are handled through an audited, secure, and compliant process. Understanding the crucial reasons you need data destruction services today is the first step toward building a more resilient security posture for your business.
Comparing On-Site vs. Off-Site Destruction for Atlanta Businesses
When it is time to destroy sensitive data, one of the primary decisions your Atlanta-based company will face is where the destruction should occur. Should you contract a vendor for mobile services, or is it more efficient to send your retired hard drives to their secure facility?
Both on-site and off-site destruction are viable options for commercial clients. The optimal choice depends on your company's security policies, compliance requirements, and budget.
Bringing the Shredder to Your Doorstep: On-Site Destruction
On-site destruction, also known as mobile shredding, involves a specialized truck equipped with an industrial-grade shredder arriving at your business location. Your hard drives, SSDs, or tapes are destroyed immediately, often under your direct supervision.
This method offers maximum transparency and is the preferred choice for organizations with zero-tolerance risk policies.
- Maximum Security: You witness the entire destruction process from start to finish. This eliminates any uncertainty about whether the task was completed correctly, providing the highest level of assurance.
- Airtight Chain of Custody: The chain of custody is minimal—your media transfers directly from your possession into the shredder, virtually eliminating transportation risks.
- Ideal for Strict Compliance: For businesses in healthcare (HIPAA), finance, or government contracting, an eyewitness account of destruction provides ironclad proof for any audit.
The main trade-off is that on-site services can be more expensive, particularly for smaller quantities of equipment. Your facility must also have adequate space for a large truck to park and operate safely.
The Practical Choice: Off-Site Data Destruction
With off-site destruction, a certified vendor collects your devices in secure, locked containers. They are then transported to a specialized, access-controlled facility where the destruction is performed.
While you do not witness the process in person, it is meticulously documented from end to end. This is often the more practical and cost-effective solution for large-scale projects, such as a data center decommissioning or an enterprise-wide hardware refresh.
A rock-solid chain of custody is paramount for off-site destruction. This includes sealed and GPS-tracked transport, documented hand-offs at every stage, and a secure facility with restricted access. It is the only way to ensure your assets are protected from the moment they leave your premises to their final destruction.
The decision tree below simplifies the choice. When managing old hardware, partnering with a certified professional is the only path that mitigates the risk of a potential data breach.
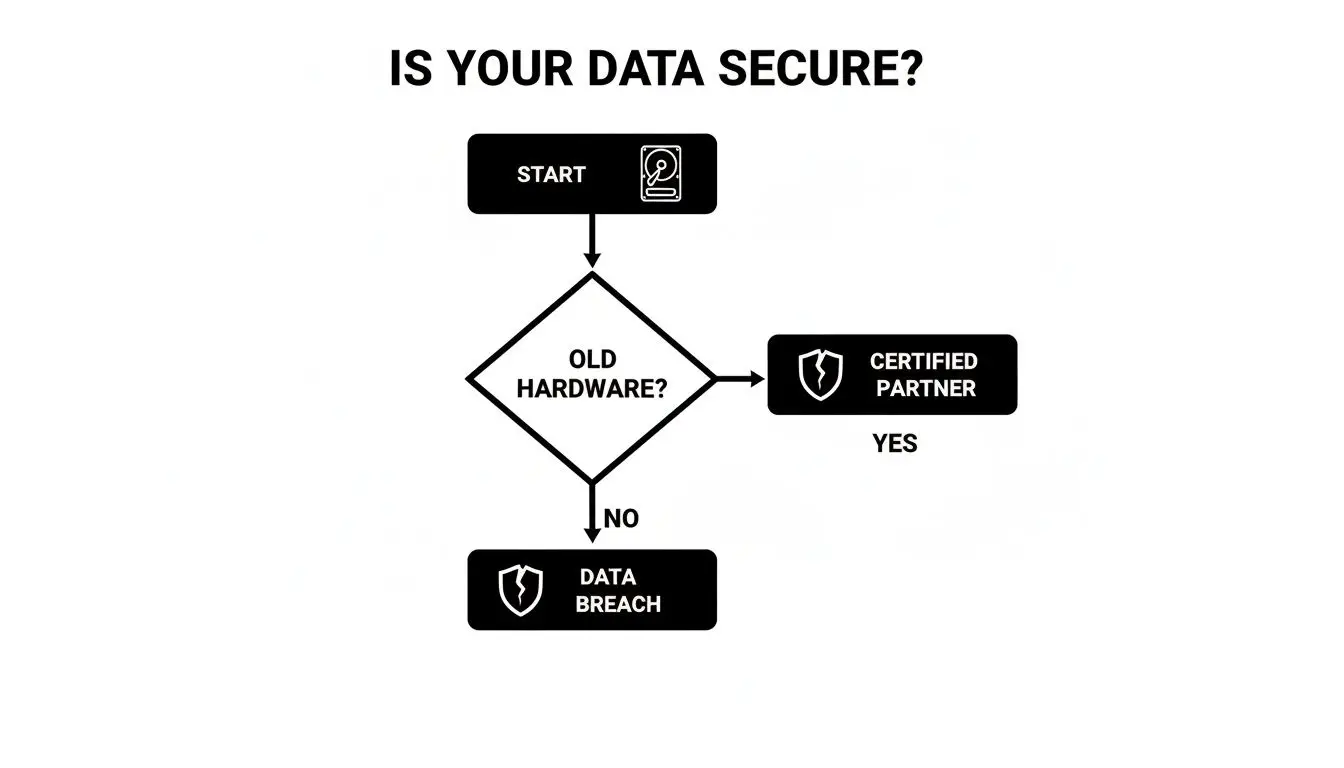
This graphic underscores a fundamental truth: without a certified process, old hardware is a ticking time bomb of liability for your business.
Making the Right Choice for Your Atlanta Business
Consider a practical example. A law firm in Atlanta handling highly sensitive client files will almost certainly require on-site shredding to obtain absolute, witnessable proof of destruction.
Conversely, a large corporation retiring 500 laptops from offices across Georgia might find off-site destruction more efficient and affordable. As long as their vendor provides a detailed, serialized Certificate of Destruction, their compliance needs are fully met.
To understand how we manage this at your location, you can learn more about our on-site data destruction services and see how we tailor the process to fit diverse business requirements.
Ultimately, the best choice depends on your organization's risk tolerance and logistical needs. A trusted partner like Beyond Surplus can guide you through these factors to determine the service that offers the right balance of security, compliance, and peace of mind for your enterprise.
Verifying Certifications and Chain of Custody
When you search for "secure data destruction near me" in Atlanta, you will discover that not all providers are created equal. Simply hiring a company is insufficient—you must verify they possess the credentials and processes to safeguard your business data. Assuming they do is a risk no enterprise can afford.
Your initial step in vetting any potential partner should be to check their industry certifications. These are not merely decorative badges for a website; they are hard-earned proof that a vendor adheres to strict, third-party standards for security and operations.
The Gold Standard: NAID AAA Certification
If one credential matters most in the data destruction industry, it is NAID AAA Certification. This is the gold standard. It is not a simple membership; it is a rigorous, ongoing audit program managed by the International Secure Information Governance & Management Association (i-SIGMA), which includes unannounced inspections.
A NAID AAA Certified company must prove it meets the highest benchmarks for:
- Employee Screening: All personnel who may come into contact with your devices have passed extensive background checks.
- Secure Processes: The entire asset journey, from pickup to final destruction, is documented and secured.
- Facility Security: Their plant is protected with access controls, continuous surveillance, and alarm systems to secure all assets until they are destroyed.
For any Atlanta business serious about data protection, selecting a NAID AAA Certified vendor should be non-negotiable. It is the clearest indicator that you are engaging a professional, verifiable, and secure operation.
Understanding the Chain of Custody
While a certification provides a baseline of trust, the real-world proof of security lies in the chain of custody. This is the official, documented paper trail that follows your IT assets from your facility to their destruction, serving as your legal and compliance shield.
A strong chain of custody is your irrefutable proof of due diligence. In the event of an audit or legal challenge, this documentation demonstrates exactly how, when, and where your sensitive data was destroyed, transferring liability to your certified partner.
For example, if a financial firm in Georgia is audited and regulators inquire about the disposal of old servers containing client data, a simple invoice is inadequate. However, if you can produce a serialized Certificate of Data Destruction linked to a detailed chain of custody record—showing sealed transport, secure facility check-in, and confirmed shredding—that inquiry is resolved immediately.
The need for this level of documentation is growing. The market for data destruction services is projected to expand from $12 billion in 2025 to a staggering $39.3 billion by 2035, driven by tougher regulations like HIPAA and CCPA. As you can see from these data destruction market findings, this growth reflects the increasing liability companies face.
Beyond NAID, other certifications like R2 (Responsible Recycling) provide an additional layer of assurance. R2 focuses on environmental compliance and data security throughout the entire electronics lifecycle. You can learn more about R2 certification in our guide to understand how it complements secure data destruction. By insisting on vendors with verifiable certifications and a transparent chain of custody, you are not just buying a service; you are investing in bulletproof risk management for your enterprise.
How to Navigate Data Privacy Regulations
Understanding data privacy regulations can feel like deciphering a complex legal code. Acronyms like HIPAA, the FTC Disposal Rule, and NIST 800-88 are frequently mentioned, but what do they mean for your business when retiring old electronics? A misstep can lead to staggering fines and significant legal challenges.
Let’s clarify these rules. These regulations are not just for large corporations; many apply to any business, regardless of size, that handles customer or employee information.
The FTC Disposal Rule Explained
Many business owners mistakenly believe the Federal Trade Commission's (FTC) Disposal Rule only applies to large financial institutions. This is a common and costly misconception. The rule mandates that any business possessing consumer reports for a business purpose must destroy them securely.
This extends beyond credit scores to include information like:
- Credit reports pulled for clients.
- Background checks conducted on potential employees.
- Reports from check-cashing services.
If this type of data resides on an old hard drive, simply deleting files is non-compliant. The FTC requires you to take "reasonable measures" to prevent unauthorized access. Professional data destruction provides a documented, compliant process that satisfies this legal standard.
HIPAA and Protected Health Information
For any organization in the healthcare sector—from hospitals and clinics to insurance companies and their business associates—the Health Insurance Portability and Accountability Act (HIPAA) is paramount. The HIPAA Security Rule is explicit about handling electronic Protected Health Information (ePHI) on end-of-life devices.
When a computer, server, or medical device containing patient data is decommissioned, you are legally required to render that data "unreadable, indecipherable, and otherwise cannot be reconstructed."
This high standard necessitates certified data wiping or physical destruction. A Certificate of Data Destruction from a certified vendor is your definitive proof of HIPAA compliance.
Why NIST 800-88 Is the Industry Benchmark
How should the data be destroyed? The National Institute of Standards and Technology (NIST) provides the technical framework. While not a law itself, its Special Publication 800-88 is the "how-to" guide for media sanitization, referenced by most regulations as the industry standard.
NIST outlines three distinct methods for sanitization:
- Clear: Involves overwriting data using standard read/write commands, as performed by some software tools.
- Purge: A more secure method of overwriting or degaussing that protects data from recovery even with advanced laboratory techniques.
- Destroy: The most absolute method—the physical destruction of storage media through shredding, crushing, or disintegration.
Any reputable data destruction partner will build their services around these NIST guidelines. For a closer look at the technical details, you can explore the NIST SP 800-88 guidelines in our detailed article.
The pressure for compliance is growing. The data destruction services market is on track to double, reaching a projected $22.84 billion by 2029 as more regulations emerge. With global cybercrime costs expected to hit $10.5 trillion annually by 2025, a data breach will cost far more than money. You can find more on this trend by reading the full market analysis.
Choosing a partner like Beyond Surplus, which operates in full accordance with these rules, provides the bulletproof documentation and peace of mind your business needs to remain compliant.
Preparing Your Business for Data Destruction Service
You have made the decision to engage professional services for secure data destruction. What are the next steps? A small amount of preparation ensures a smooth process, an accurate quote, and a rock-solid chain of custody.
Let's review how to organize your assets for service.
Getting an Accurate Quote Starts With an Inventory
Before you can receive a reliable quote, you need to know what you have. A simple inventory is sufficient.
A tally such as "45 desktops, 15 laptops, and 1 box of 100 loose hard drives" provides a vendor with the necessary information to price your project accurately. Without this basic count, any quote is merely a guess.
When you receive quotes, they will likely follow one of these pricing models:
- Priced per drive: A flat rate for each hard drive, SSD, or tape, common for smaller projects.
- Priced by weight: Often used for large volumes of media where individual counting is impractical.
- A flat project fee: Typical for complex jobs like a full data center decommissioning, which includes labor for de-installing servers.
Ensure you understand the pricing model and inquire about potential additional charges, such as travel fees or costs for serialized reporting.
How to Prepare Your Office Before Pickup
Once you have scheduled the service, internal organization can streamline the process. The most critical step is to consolidate all equipment into a single, secure area. This prevents confusion and ensures no devices are overlooked.

It is also wise to assign a single point of contact from your team to manage the handover. This individual will officially release the assets, sign the initial chain-of-custody forms, and serve as the main liaison for the vendor’s team on-site. For additional tips, you can review our guide on how to prep electronics for recycling.
Insider Tip: If time permits, separate items by type—loose hard drives, laptops, servers, etc. This detail helps the vendor work more efficiently and ensures your final inventory report is clean and accurate.
Whether coordinating a nationwide pickup, dropping off items locally in the Atlanta area, or using a mail-in program for a small batch of drives, these steps ensure the job is done right, providing you with a clear, documented, and secure process from beginning to end.
Common Questions About Secure Data Destruction for Businesses
Even with a solid plan, it is normal for business owners and IT managers to have questions before handing over sensitive corporate data. Getting clear answers is essential for confidence in your chosen vendor. Let's address some of the most common concerns.
Is Data Wiping as Secure as Physical Shredding?
Yes, both methods are extremely secure when performed by a certified professional. The best method depends on your equipment's age and your company’s internal security policies.
Certified data wiping, adhering to standards like NIST 800-88, uses specialized software to overwrite every sector of a drive, making the original data completely unrecoverable. This is an excellent option for newer, functional hard drives and SSDs as it preserves their value for refurbishment and reuse.
Physical shredding is the ultimate form of data destruction. The drive is physically disintegrated into small metal fragments, making data recovery impossible. This is the preferred method for failed or obsolete drives, or when corporate policy demands undeniable visual proof of destruction. A qualified partner can help you implement a hybrid approach, using the right method for each asset.
What Documentation Should My Business Receive After the Service?
You must always receive a formal Certificate of Data Destruction. This document is your official proof of compliance with laws like the FTC Disposal Rule and HIPAA. Crucially, it legally transfers liability for that data from your company to your vendor.
A Certificate of Data Destruction is not just a piece of paper; it is your auditable proof of due diligence. Without it, your business has no way to prove to regulators that its sensitive data was destroyed correctly.
Ensure the certificate is detailed and includes:
- The date and specific method of destruction (e.g., wiping or shredding).
- A serialized list of the hard drives or other assets destroyed.
- A unique job or reference number linked to your chain-of-custody paperwork.
Are Professional Services Available for a Small Business?
Absolutely. Data security is not exclusively a large-corporation issue. In fact, small and medium-sized businesses are often targeted because they are perceived to have weaker security controls. Regulations like the FTC Disposal Rule apply to all businesses that handle consumer data, regardless of size.
Many professional data destruction companies, including Beyond Surplus, offer flexible and affordable options for smaller businesses in the Atlanta area. We have designed our services to accommodate smaller jobs, including:
- Convenient drop-off locations for just a few drives at a time.
- Secure mail-in programs that provide a cost-effective nationwide solution.
These commercial services give any business access to the same enterprise-grade security as a Fortune 500 company, ensuring complete protection.
Contact Beyond Surplus for certified electronics recycling and to schedule your secure IT asset disposal service. Explore our commercial services at https://westhilldentalpeaceriver.com.