Thinking about retiring a server in your New York City, NY business? It’s not as simple as just unplugging it and shoving it in a storage closet. Proper server decommissioning is a critical business operation, one that shields your company from serious financial and legal blowback, like data breaches and compliance failures. For enterprises in New York City, a strategic approach to IT asset disposal is essential for maintaining data security and regulatory compliance.
Why Your Server Decommissioning Plan Matters
Treating server decommissioning as a simple IT chore instead of a strategic process is a mistake with huge implications for your company's security, compliance, and even your budget. Without a formal plan, that retired server sitting in the corner can quickly become a liability. We've seen it happen time and again—forgotten assets still loaded with sensitive data, just waiting for a breach.
A well-structured plan flips this script, turning a risky task into a controlled, secure, and sometimes even profitable procedure. It’s your best defense against the expensive fallout from improper IT asset disposal.
The High Stakes of Getting It Wrong
The financial and reputational damage from a bungled server retirement can be staggering. In fact, mishandled decommissioned servers are a common culprit behind sensitive data leaks, and the stakes are higher than ever. The average global cost of a data breach has now hit $4.45 million, a number that should make any executive pause and think about the true cost of a security lapse.
On top of that, with US businesses tossing out millions of tons of electronics every year, the regulatory and environmental pressures are only getting stronger.
A single server that isn't disposed of correctly can lead to:
- Costly Data Breaches: Think about it—customer data, intellectual property, or financial records left on a drive are low-hanging fruit for bad actors. You can learn more about how to prevent data breaches from improper equipment disposal.
- Hefty Compliance Fines: Regulations like HIPAA, GDPR, and SOX don't mess around when it comes to data handling and destruction. Non-compliance can trigger penalties that make the cost of professional decommissioning look like pocket change.
- Environmental Penalties: E-waste is a heavily regulated space. Just dumping a server can land you with fines for breaking environmental laws.
A server decommissioning plan isn’t an expense; it’s an insurance policy. It formally transfers liability, creates an auditable record of data destruction, and ensures every step is compliant with industry and environmental standards.
Turning Risk into Opportunity
On the flip side, a smart decommissioning strategy does more than just sidestep risks. It lets you transform a potential liability into a real asset for your business.
A solid plan means you can:
- Recover Value from Hardware: Newer or still-functional components can be refurbished and resold through IT Asset Value Recovery (ITAVR) programs. This can generate revenue that helps offset the project's costs.
- Meet Sustainability Goals: When you work with certified recyclers like Beyond Surplus, you ensure old hardware is handled in an environmentally responsible way, which is a great boost for your corporate social responsibility (CSR) initiatives.
- Maintain a Secure Audit Trail: Getting a Certificate of Data Destruction and detailed chain-of-custody documents gives you undeniable proof of due diligence. This protects your organization from any future claims or questions.
Ultimately, approaching server decommissioning with a strategic mindset is about turning a necessary end-of-life process into a secure, compliant, and strategic win for your business.
Building Your Pre-Decommissioning Blueprint
Trying to decommission a server without a rock-solid plan is like trying to navigate a minefield blindfolded. It's a recipe for disaster. Before you even think about unplugging a single cable, you need a comprehensive blueprint. This plan becomes your North Star, making sure every move is deliberate, secure, and lines up with what the business actually needs.
Without one, you're just inviting chaos. With a good plan, you turn a messy technical task into a controlled, predictable process.
The very first step? Assembling a cross-functional team. This isn't just an IT job; it touches multiple parts of the business, and you need their buy-in and expertise from day one. Your core team should have people from:
- IT Operations: These are your boots on the ground for the technical execution, data migration, and actually handling the hardware.
- Cybersecurity: They'll be watching over the data destruction to make sure you're compliant and not accidentally creating a security hole.
- Finance: Someone needs to track the asset's depreciation, manage the budget for disposal, and account for any cash you get back from reselling parts.
- Facilities Management: Especially in a packed data center, you need them to coordinate the physical removal of the servers.
Thinking it through methodically is everything. It's a lot like following an employee termination process checklist—both processes are loaded with risk, and a structured approach is the only way to get it right.
Asset Inventory and Dependency Mapping
Once your team is ready, it's time for a deep dive into what you're actually dealing with. You absolutely have to know every detail about the server and how it connects to your environment before you can safely pull the plug. A proper inventory is way more than just a model number.
Your inventory checklist should capture:
- Hardware Specifications: CPU, RAM, storage, network cards—the full spec sheet.
- Software and Licenses: What OS is it running? What applications? Are there licenses we can reclaim or need to transfer?
- Data Classification: What kind of data is on this thing? Is it sensitive PII, critical financial records, or valuable intellectual property?
Honestly, the toughest part is almost always the dependency mapping. This is where you trace every single connection, both incoming and outgoing, to figure out what other applications, services, or servers will break when this one goes dark. Pulling the plug on a server that, unbeknownst to you, handles authentication for a critical app can cause a massive, embarrassing, and completely avoidable outage. Having strong IT asset management best practices in place makes this infinitely easier.
The single biggest mistake we see is underestimating dependencies. A server rarely lives in isolation. Meticulously mapping its data flows and service connections is the most effective way to prevent unexpected disruptions during the shutdown process.
The risks of getting this wrong are very real. The diagram below shows exactly what can happen when a decommissioning process is rushed or sloppy.
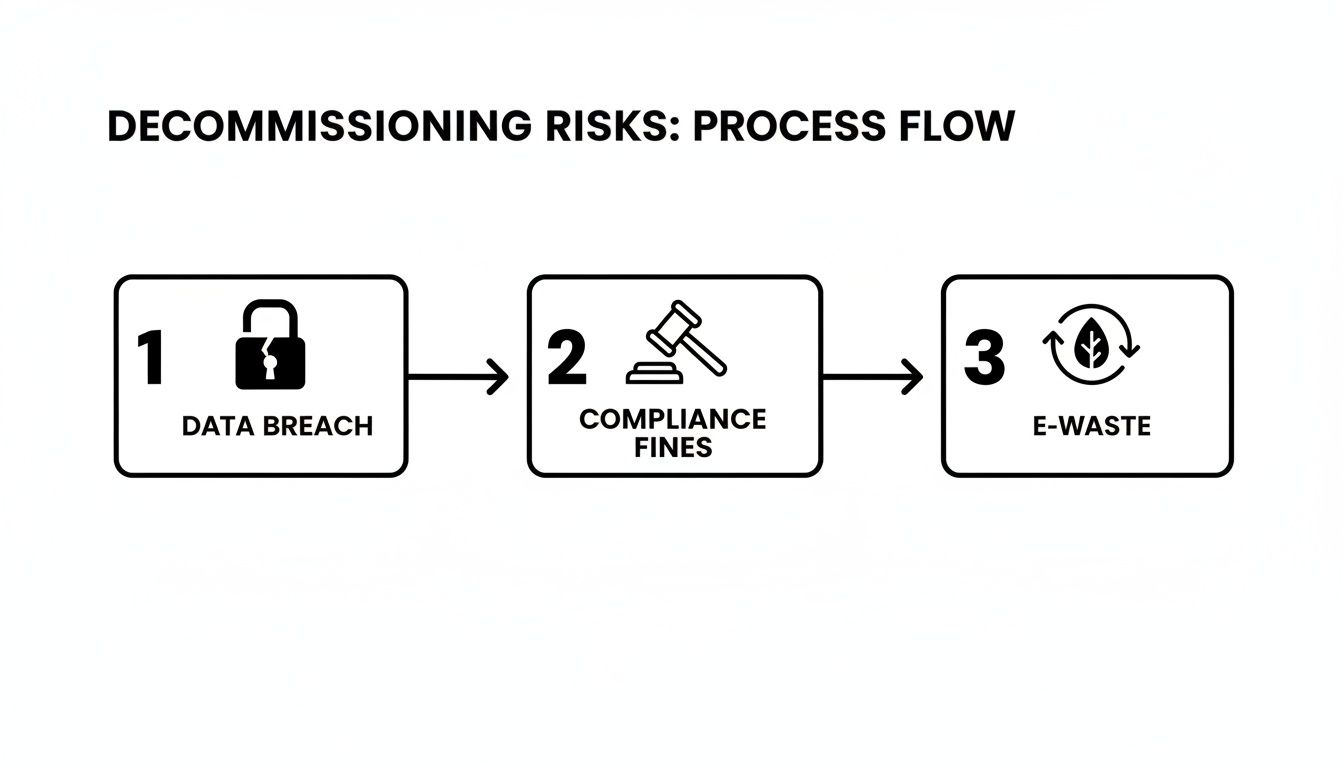
As you can see, a simple planning failure can quickly cascade into a data breach, which then brings on compliance fines and contributes to the growing e-waste problem. It's all connected.
Defining Timelines, Budgets, and Roles
With a clear inventory and dependency map, you can start building out the rest of your blueprint. Now it's about getting practical. Set a realistic timeline that accounts for every single stage, from the initial data migration and verification all the way to the physical hardware removal and final sign-off.
Next up is the budget. Don't forget to account for costs like labor, any new hardware or cloud services you'll need for the migrated apps, and the fees for a certified ITAD partner like Beyond Surplus to handle the secure data destruction and electronics recycling.
Finally, assign crystal-clear roles and responsibilities. Who is ultimately accountable for each task? Who communicates downtime to stakeholders? Who signs the certificate of data destruction? When everyone knows exactly what they're responsible for, you eliminate confusion and pave the way for a smooth, successful project.
Executing the Shutdown and Data Migration
Alright, you've done the homework and have a solid blueprint in hand. Now it's time to move from theory to practice. This is the stage where all that meticulous planning really starts to pay off, turning what could be a chaotic mess into a series of controlled, deliberate steps. It’s go-time for migrating services, securing data, and methodically prepping the server for its final journey.
This isn't about just yanking a power cord and calling it a day. We're talking about a systematic shutdown of services, a careful transfer of every last byte of data, and crystal-clear communication to keep the business running smoothly. The end goal is simple: a seamless transition with zero data loss and practically no impact on your end-users.

Getting Data and Workloads Moved
First things first: we need to get the server’s data and workloads to their new home. Whether you're moving to another physical box, a VM, or making the leap to the cloud, the core principles of data integrity don't change. This isn't a simple copy-paste job; it's a delicate operation.
A bulletproof migration strategy always includes:
- Final Full Backup: Before you touch anything, run one last, complete backup of everything on the server. Think of this as your ultimate safety net.
- Data Transfer: Use the right tools for the job. This could be a live network transfer for minimal downtime or restoring that final backup into the new environment.
- Verification and Testing: This part is absolutely non-negotiable. Once the data is moved, you have to verify that 100% of it made the trip correctly and is working as expected. Test the apps, ping the databases, and run your validation scripts to confirm everything is intact.
Nailing the Downtime Communication
No server lives in a bubble. Your dependency map should have already told you exactly who and what will be affected when this machine goes offline. Proactive, clear communication is what separates a smooth maintenance window from a frantic "everything is down!" fire drill.
Your communication plan needs to be simple and direct:
- What's happening? Briefly explain that a specific server is being retired.
- When is it happening? Give a precise schedule, including start and end times.
- What will be affected? List the specific services or applications that will be unavailable.
- Who do they call? Designate a clear point of contact for any issues.
A well-communicated downtime is just planned maintenance. A poorly communicated one feels like a surprise outage. The difference in user perception is huge and directly reflects on your IT team's credibility.
When you're dealing with bigger projects, like taking out entire racks or more, these same principles just scale up. Often, a single server retirement is just one piece of a much larger puzzle. To get a feel for the bigger picture, it helps to understand the complexities of decommissioning a data center.
The Step-by-Step Shutdown Procedure
Once you've confirmed the data is safely migrated, verified it's all working, and notified everyone involved, you can finally proceed with the shutdown. This is a methodical sequence, not a sudden power cut. Following a structured process ensures the server goes offline cleanly, preventing any last-minute data corruption or hardware headaches.
Here’s the typical shutdown sequence I follow:
- Stop Services and Applications: Gracefully stop all running software to make sure they terminate correctly and write any final data.
- Disconnect from the Network: Isolate the server completely. Disable its network interfaces or just physically unplug the ethernet cables.
- Log Off Users: Double-check that all active user sessions have been terminated.
- Initiate OS Shutdown: Use the operating system’s proper shutdown command. Let it power down gracefully.
- Physical Disconnection: After the server is completely powered off and silent, you can safely unplug the power cords, KVM switches, and anything else still connected.
Following this structured approach ensures the server is safely and securely ready for what comes next: data destruction and physical removal.
Ensuring Secure and Permanent Data Destruction
Once the data is migrated and the servers are powered down, you’ve reached the most critical security phase of the entire decommissioning process. This is where the focus shifts from operational continuity to total risk elimination. I've seen it happen too many times: leaving residual data on retired hard drives isn't just a simple oversight—it's a massive security hole waiting to be exploited.
This step is all about making sure every last bit of sensitive information is gone for good, completely and permanently irrecoverable.
Simply deleting files or formatting a drive doesn't cut it. Not even close. Data recovery software can easily pull information from drives that have only been superficially wiped. Real data destruction demands deliberate, verifiable methods that stand up to tough industry standards.

Choosing Your Data Sanitization Method
The right method really comes down to your data's sensitivity, your compliance needs (like HIPAA or SOX), and whether you plan to reuse the drives or just get rid of them. Your options fall into two main camps: software-based wiping and physical destruction.
Software-Based Wiping (Data Erasure)
This approach uses specialized software to overwrite every sector of a hard drive with random characters, effectively sanitizing it. For higher security needs, the software can run multiple passes to meet specific protocols.
- When to Use It: This is the perfect choice for drives you plan to redeploy somewhere else in your organization or resell to recover some value.
- Key Standard: The absolute gold standard here is NIST 800-88. Following these guidelines ensures data is forensically unrecoverable. For a deeper dive, you can learn more about the specifics of NIST SP 800-88 compliance.
Physical Destruction
When data is extremely sensitive, or the drives are old and failing, physical destruction is the only way to be 100% certain that data can never be accessed again. There's no coming back from this.
- Degaussing: A degausser blasts the drive with a powerful magnetic field, scrambling the magnetic platters and instantly destroying all data. It also renders the drive totally inoperable.
- Shredding: This is the most secure and visually satisfying method. The hard drives are fed into an industrial shredder that grinds them into tiny, unsalvageable metal fragments.
Choosing between these methods is a crucial part of any data destruction plan. To make it clearer, here's a quick comparison.
Comparing Data Destruction Methods
| Method | Security Level | Best For | Certificate of Destruction Provided |
|---|---|---|---|
| Software Wiping (NIST 800-88) | Very High | Reusing or reselling drives; meeting compliance standards. | Yes |
| Degaussing | Extremely High | End-of-life drives with highly sensitive data. Renders drive unusable. | Yes |
| Shredding | Absolute/Physical | Maximum security; end-of-life drives; visual verification is required. | Yes |
Ultimately, the right choice ensures you’re not just destroying data, but also adhering to your industry's compliance standards and overall risk management strategy. A good understanding of broader data security best practices will help you build a more resilient security posture across the board.
The Importance of On-Site vs. Off-Site Destruction
Deciding where the destruction happens is another key security decision. Both on-site and off-site services can be secure, but your organization's risk tolerance might make one a better fit.
- On-Site Destruction: A mobile shredding truck comes right to your facility. You can literally watch your drives get turned into confetti. This offers maximum peace of mind because the chain of custody is as short as it gets—from your server room straight into the shredder.
- Off-Site Destruction: The assets are packed into locked, sealed bins at your location and transported by a secure, GPS-tracked vehicle to a certified facility for destruction. It’s often more cost-effective for large volumes, and with a trusted ITAD partner, the chain-of-custody is meticulously documented every step of the way.
The Certificate of Data Destruction is not just a receipt. It is a legal document that formally transfers liability from your organization to your ITAD vendor, providing an indispensable audit trail for compliance purposes.
Why the Certificate of Destruction is Non-Negotiable
No matter which method you choose, the process absolutely must end with the issuance of a Certificate of Data Destruction. This is your official, legal proof that the data was destroyed securely and in a compliant manner.
The certificate should list the specific serial numbers of the destroyed drives, the date, location, and the method used.
Without this document, you have zero verifiable proof of due diligence. If an auditor comes knocking or you face a legal challenge, this certificate is your first line of defense. It proves you took the necessary, professional steps to protect sensitive information. This has become even more critical as the industry grows; the data center decommissioning service market is projected to surge to over $15 billion by 2033, driven by the need to manage e-waste securely and sustainably.
The Final Step: IT Asset Disposition (ITAD)
With all the data wiped clean and security risks handled, the server decommissioning process shifts from the digital world to the physical one. Your server is now just a piece of hardware. So, what do you do with it? This is where professional IT Asset Disposition (ITAD) comes in, making sure the final chapter of your server's life is handled responsibly, legally, and with an eye on your bottom line.
The first step is getting the hardware out of the rack. This means carefully un-racking the server, meticulously disconnecting and labeling every cable, and getting the unit ready for secure transport. It's less about tech skills and more about methodical, careful work, especially if you hope to resell some of the components.
The Two Paths of IT Asset Disposition
Once a server is prepped for removal, it will head down one of two main paths. The right path depends on its age, condition, and whether there's any demand for it on the secondary market. Either way, you'll need to partner with a certified ITAD vendor to guarantee a secure chain of custody and full compliance.
- Responsible E-Waste Recycling: If you're dealing with older servers that have little to no resale value, the top priority is environmentally sound disposal.
- IT Asset Value Recovery (ITAVR): For newer or high-demand hardware, the goal is to refurbish and resell components to recoup some of your initial investment.
A good ITAD partner has the experience to assess each asset and steer you toward the most logical and profitable option.
Certified Recycling for Environmental Compliance
For hardware that has truly seen its last days, tossing it in a landfill is out of the question. It’s not just environmentally reckless; it's illegal in many places. The only real solution is to work with a recycler certified under standards like R2 (Responsible Recycling) or e-Stewards.
Think of these certifications as your guarantee that the vendor follows strict rules for environmental protection and data security.
Partnering with a certified e-waste recycler is a non-negotiable part of modern IT governance. It provides a documented, auditable trail that proves your organization disposed of electronic assets in full compliance with local, state, and federal environmental regulations, effectively mitigating legal and reputational risk.
A certified vendor will break down the server, separating materials like steel, aluminum, and plastic for recycling. They also know how to safely manage hazardous materials like the lead and mercury found on circuit boards, ensuring they don't end up poisoning the environment.
Recovering Value Through Remarketing
Now, if your servers are only a few years old, there’s a good chance they still have significant value locked inside their components. This is where IT Asset Value Recovery (ITAVR) shines. A skilled ITAD partner can test, refurbish, and find buyers for valuable parts like:
- CPUs
- RAM modules
- High-capacity hard drives (after they’ve been securely sanitized, of course)
- Network interface cards (NICs)
- Power supply units (PSUs)
The money you make from selling these components can be surprisingly substantial. We've seen many organizations use these funds to offset the entire cost of the decommissioning project—covering labor, data destruction, and transport. It turns a necessary expense into something that's budget-neutral or even profitable.
This whole process of turning retired gear into a financial asset is a core part of ITAD. If you want to dig deeper into the framework, you can explore this detailed guide on what IT asset disposition is and see how it can work for your organization.
Ultimately, whether you're recycling responsibly or remarketing strategically, a professional ITAD program ensures your decommissioned server hardware is managed securely, sustainably, and for the maximum financial benefit to your business.
Finalizing the Project: Documentation and Cleanup
You've pulled the plug, wiped the drives, and waved goodbye to the physical hardware. It feels like the project is over, but don't close the ticket just yet. We've now hit the final, and arguably most critical, phase: the administrative wrap-up.
This is where you build the paper trail that proves you did everything by the book. Think of it as your organization's defense against any future compliance audits or legal questions. Without this, all that careful technical work could be undermined.
A project isn't truly done until the paperwork is filed and signed off.
Building Your Definitive Audit Trail
Your main goal here is to create a complete project archive. This isn't just busywork; it's a historical record that someone might need to pull up months or even years from now during an audit. It needs to tell the full story, from start to finish, with no gaps.
Here's the essential documentation you need to pull together:
- The Original Project Plan: This is your starting point. It shows the initial scope, who signed off on it, and what the timeline was supposed to be.
- Finalized Asset Inventory: You need a crystal-clear list of what, exactly, was decommissioned. This means serial numbers, asset tags, and hardware specs all confirmed and accounted for.
- Chain-of-Custody Reports: Your ITAD partner provides this. It’s the official log that tracks each asset from the second it leaves your building to its final destination.
- Certificate of Data Destruction: This is the big one. It's the legal document that certifies all data was destroyed permanently, following specific standards like NIST 800-88. This is non-negotiable.
This packet of documents is more than just procedural—it's your liability shield. It's the undeniable proof of a systematic, compliant, and defensible process for handling your end-of-life IT assets.
Crafting the Final Decommissioning Report
Once you have all the core documents, it's time to create a high-level summary report. This is the document that goes to leadership and stakeholders. It’s the final sign-off that officially closes the loop on the entire project, confirming everything went as planned.
Keep it concise. Your final report should summarize:
- Project Outcomes: A simple confirmation that the server was decommissioned successfully, on time, and on budget.
- Service Migration Confirmation: Verification that every application and service was moved to its new home and is running without issues.
- Financial Reconciliation: A quick breakdown of any money recovered from selling the old hardware, measured against the project's total costs.
Performing the Final System Clean-Up
Last but not least, a little digital housekeeping ensures the old server is completely gone from your environment, preventing it from haunting you later.
Start by updating your CMDB or asset management system. Formally mark the server as "retired." This one simple step prevents it from showing up as a "ghost asset" in future security scans or inventory audits, which can save your team a lot of headaches.
Next, take a look at software licenses. Was there any software tied specifically to that old server? You might be able to reclaim those licenses and reassign them, which is a quick way to save the company some money. It's these small finishing touches that separate a good project from a great one.
Answering Your Server Decommissioning Questions
Even with a solid playbook in hand, a few questions almost always pop up when it's time to retire old servers. Let's tackle some of the most common ones I hear from IT managers and business owners. Getting these cleared up can save a lot of headaches down the road.
How Long Does It Take to Decommission a Server?
This is the classic "it depends" scenario, but the timeline really does swing wildly based on the server's role.
For a simple, standalone file server that isn't tangled up with other systems, you might be looking at just a few days from start to finish. But for a critical application server that's the backbone of your operations? That's a different story. Decommissioning something that deeply embedded can easily turn into a multi-month project. You'll need to account for meticulous planning, a carefully managed data migration, and then rigorous testing to make sure everything works perfectly before you pull the final plug.
What Is the Difference Between Data Wiping and Physical Destruction?
Both methods get the job done, but they're suited for different situations. Think of it as the difference between securely clearing a house and demolishing it.
-
Data Wiping: This is a software-based approach. Specialized tools overwrite every single sector of a hard drive with random data, making the original information forensically unrecoverable. The big win here is that the drive itself is still perfectly good and can be reused or resold, helping you recover some value.
-
Physical Destruction: This is exactly what it sounds like. Industrial shredders grind the drives into tiny metal fragments, making data recovery completely impossible. This is the go-to for the highest level of security and is often a non-negotiable requirement for drives that held regulated or extremely sensitive information.
While you can handle some of the initial planning in-house, the risks tied to improper data destruction are huge. Honestly, it almost always outweighs the cost of bringing in a certified pro. A certified ITAD vendor gives you an insured, auditable process that truly protects your company.
Can We Handle Server Decommissioning In-House to Save Money?
I understand the temptation to DIY this to cut costs, but this is one area where trying to save a few bucks can backfire spectacularly. A single slip-up can lead to a devastating data breach or a massive compliance fine that makes any initial savings look tiny.
This is why partnering with a certified ITAD vendor is a smart business decision, not just an IT one. They bring the expertise, the specialized equipment, and—most importantly—the paperwork. That Certificate of Data Destruction is your proof. It creates a defensible audit trail that ensures you are fully shielded from liability.
For secure, compliant, and efficient server decommissioning services in New York City, NY, trust the experts. Beyond Surplus provides certified electronics recycling and secure IT asset disposal for businesses nationwide. Contact us today to schedule your pickup and protect your data.